A true web application firewall for WordPress.
| Author: | The Ninja Technologies Network (profile at wordpress.org) |
| WordPress version required: | 4.9 |
| WordPress version tested: | 6.5 |
| Plugin version: | 4.5.11 |
| Added to WordPress repository: | 30-03-2013 |
| Last updated: | 17-03-2024 |
| Rating, %: | 96 |
| Rated by: | 204 |
| Plugin URI: | https://nintechnet.com/ |
| Total downloads: | 2 065 510 |
| Active installs: | 100 000+ |
 Click to start download |
|
A true Web Application Firewall
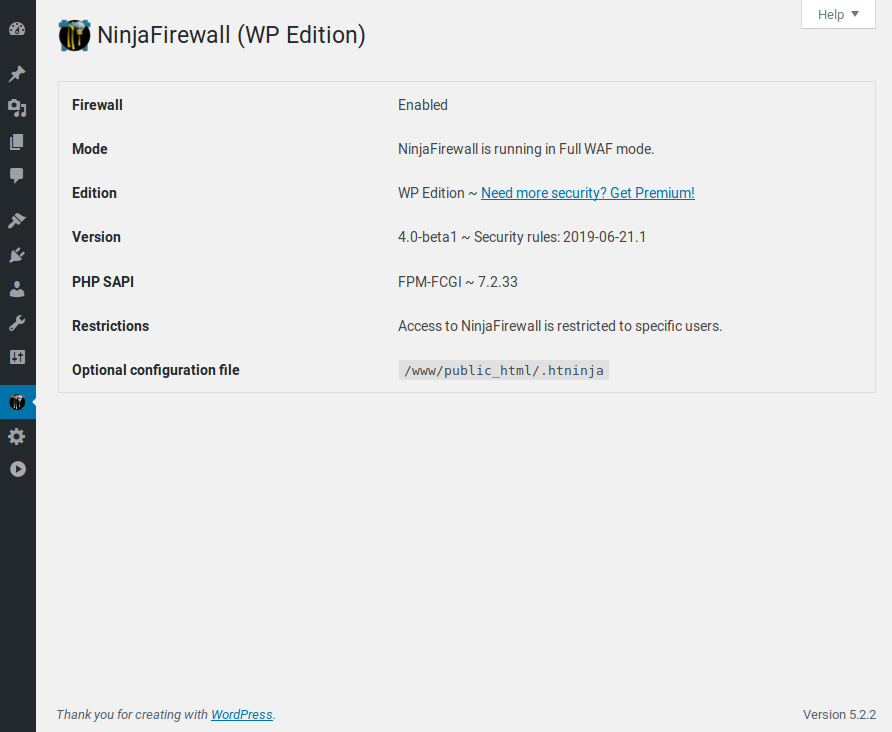
NinjaFirewall (WP Edition) is a true Web Application Firewall. Although it can be installed and configured just like a plugin, it is a stand-alone firewall that stands in front of WordPress.
It allows any blog administrator to benefit from very advanced and powerful security features that usually aren’t available at the WordPress level, but only in security applications such as the Apache ModSecurity module or the PHP Suhosin extension.
NinjaFirewall requires at least PHP 7.1, MySQLi extension and is only compatible with Unix-like OS (Linux, BSD). It is not compatible with Microsoft Windows.
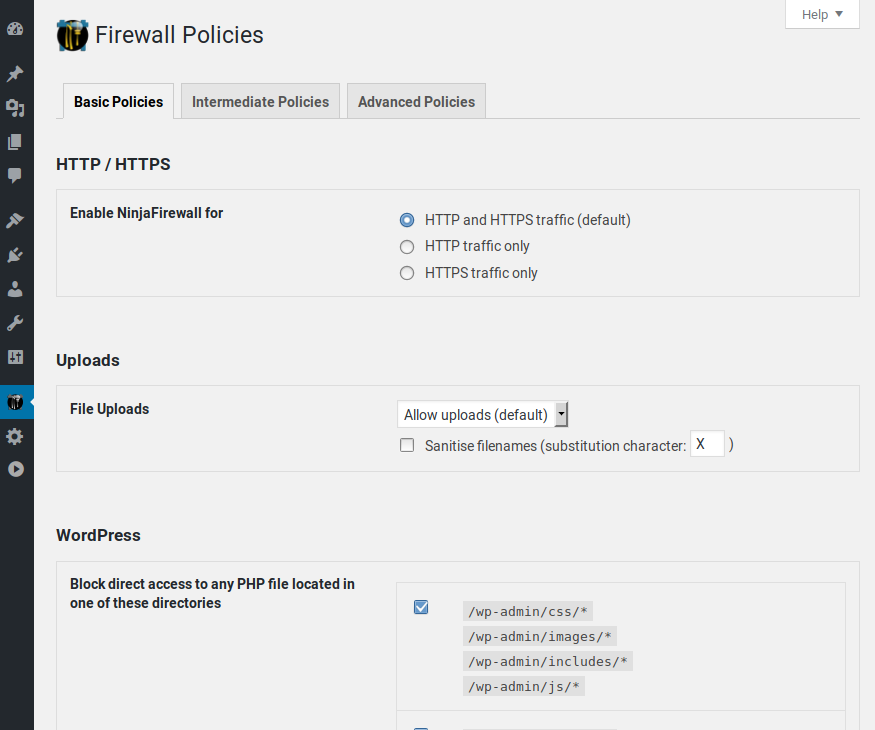
NinjaFirewall can hook, scan, sanitise or reject any HTTP/HTTPS request sent to a PHP script before it reaches WordPress or any of its plugins. All scripts located inside the blog installation directories and sub-directories will be protected, including those that aren’t part of the WordPress package. Even encoded PHP scripts, hackers shell scripts and backdoors will be filtered by NinjaFirewall.
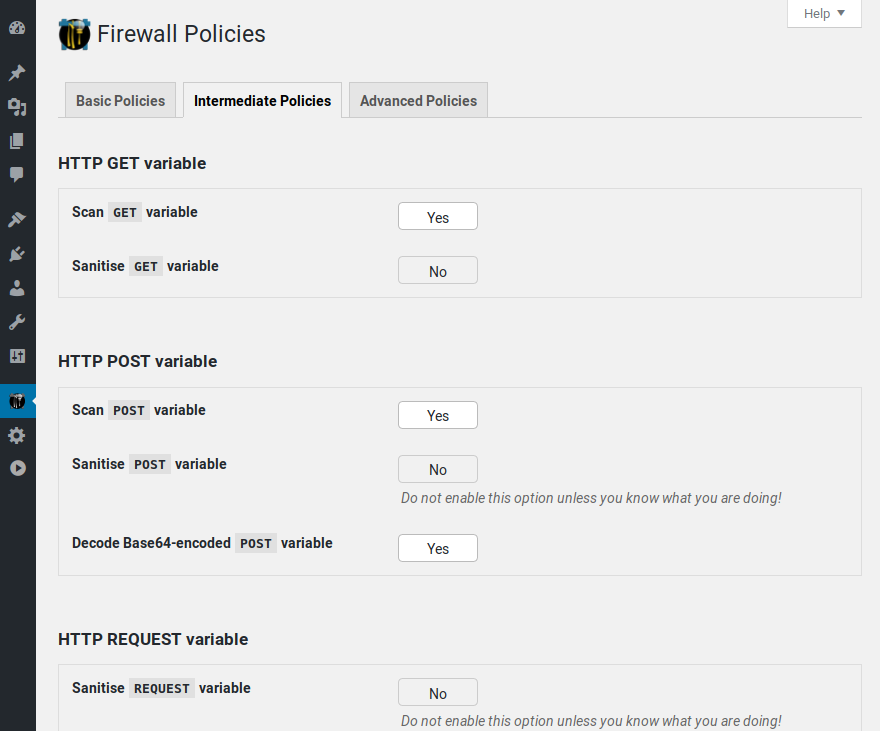
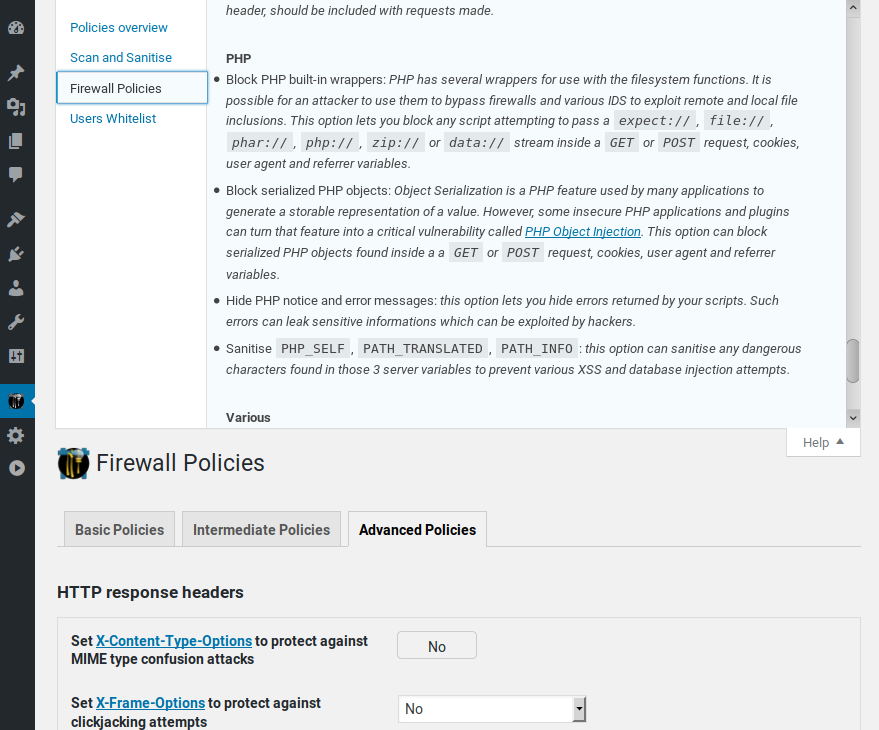
Powerful filtering engine
NinjaFirewall includes the most powerful filtering engine available in a WordPress plugin. Its most important feature is its ability to normalize and transform data from incoming HTTP requests which allows it to detect Web Application Firewall evasion techniques and obfuscation tactics used by hackers, as well as to support and decode a large set of encodings. See our blog for a full description: An introduction to NinjaFirewall filtering engine.
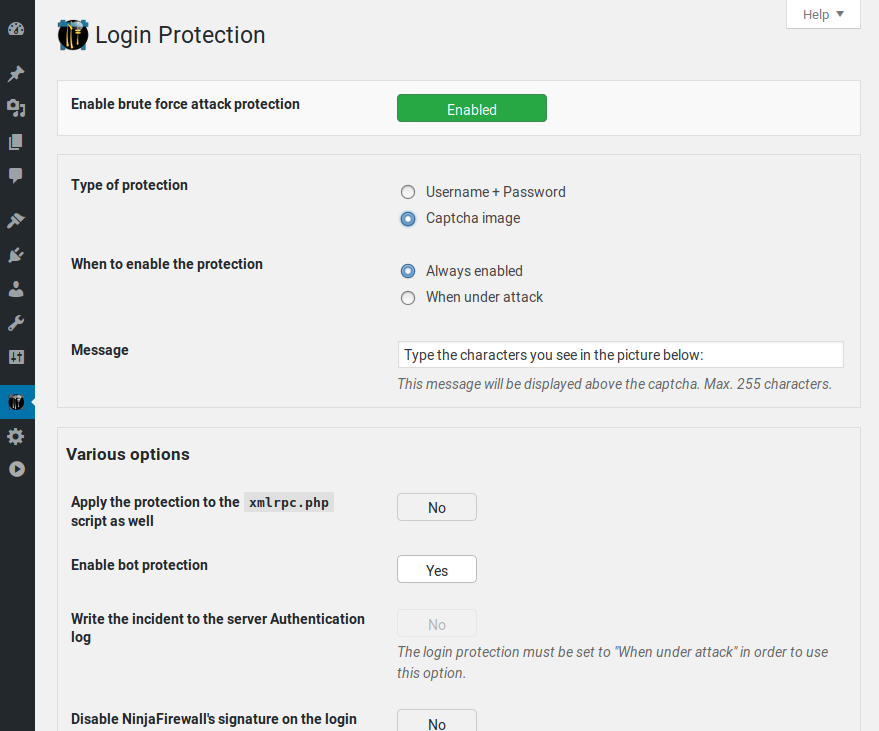
Fastest and most efficient brute-force attack protection for WordPress
By processing incoming HTTP requests before your blog and any of its plugins, NinjaFirewall is the only plugin for WordPress able to protect it against very large brute-force attacks, including distributed attacks coming from several thousands of different IPs.
See our benchmarks and stress-tests: Brute-force attack detection plugins comparison
The protection applies to the wp-login.php script but can be extended to the xmlrpc.php one. The incident can also be written to the server AUTH log, which can be useful to the system administrator for monitoring purposes or banning IPs at the server level (e.g., Fail2ban).
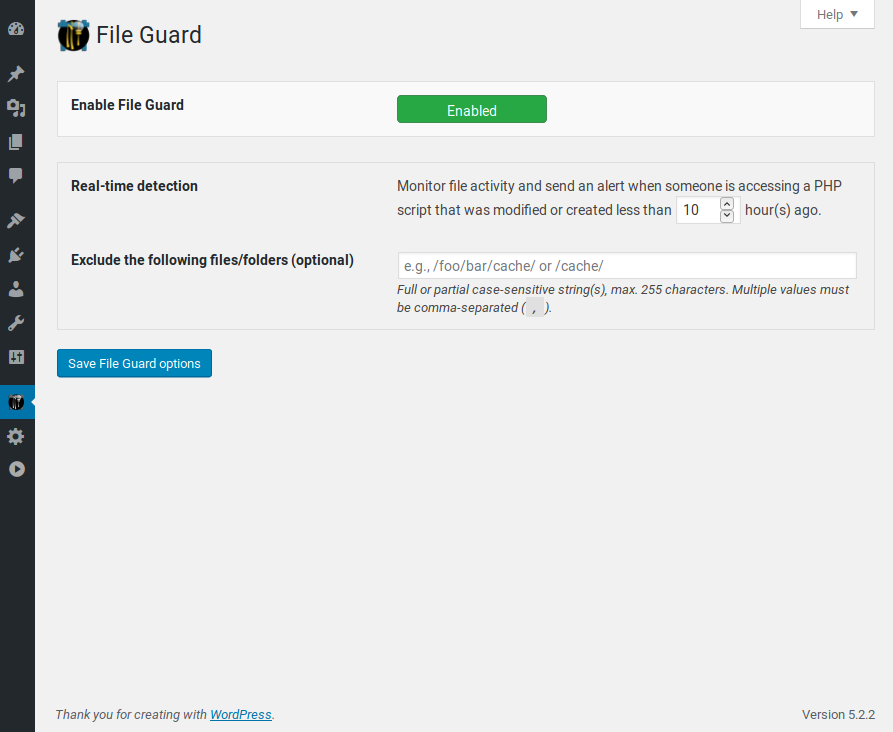
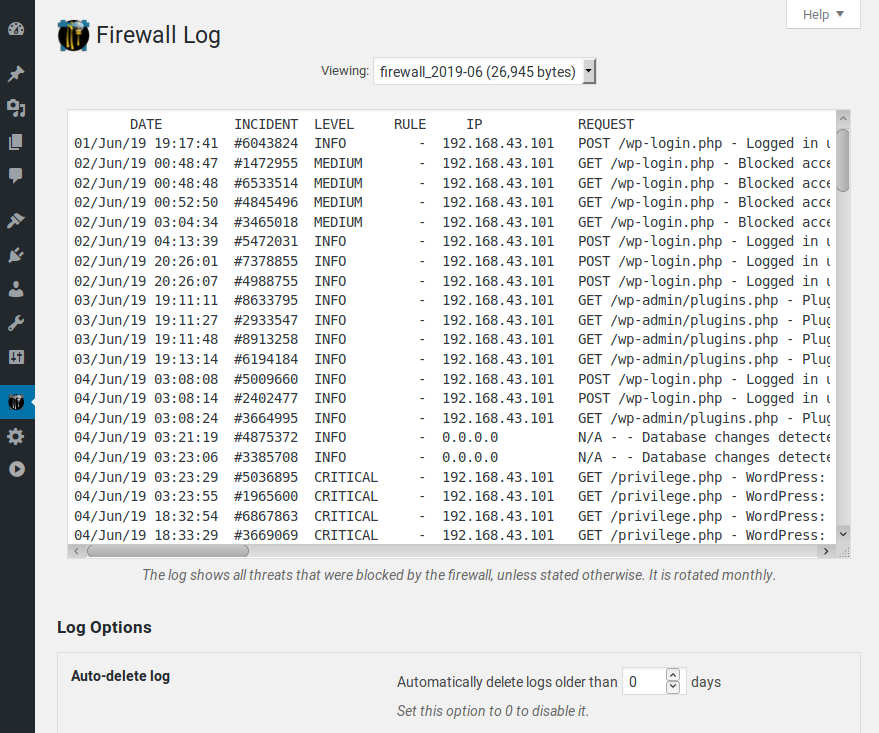
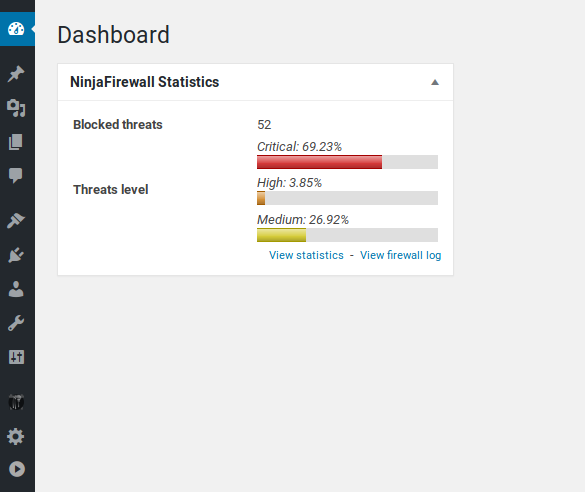
Real-time detection
File Guard real-time detection is a totally unique feature provided by NinjaFirewall: it can detect, in real-time, any access to a PHP file that was recently modified or created, and alert you about this. If a hacker uploaded a shell script to your site (or injected a backdoor into an already existing file) and tried to directly access that file using his browser or a script, NinjaFirewall would hook the HTTP request and immediately detect that the file was recently modified or created. It would send you an alert with all details (script name, IP, request, date and time).
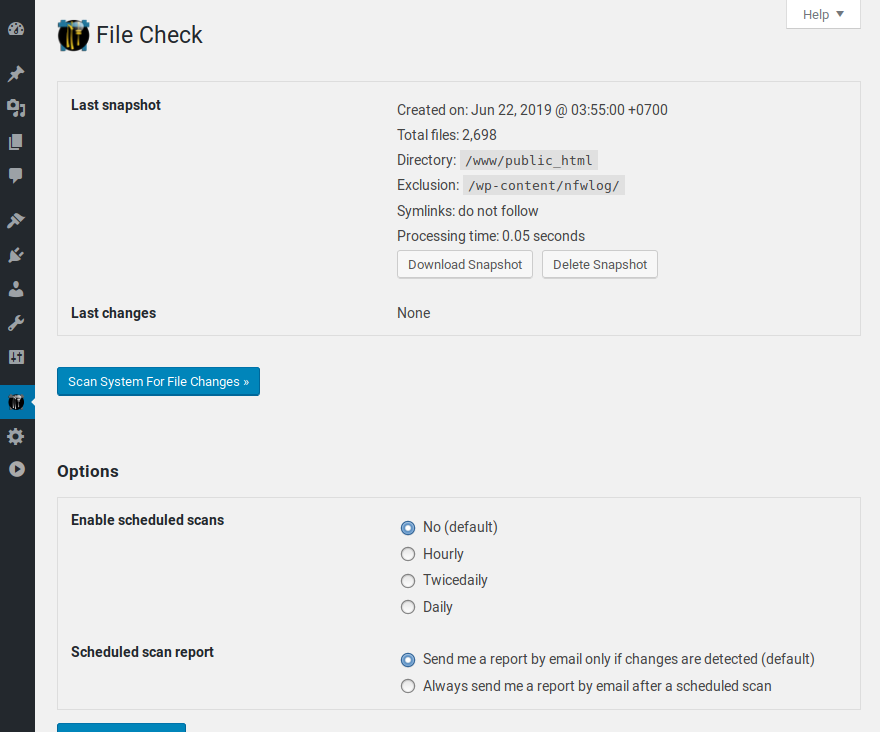
File integrity monitoring
File Check lets you perform file integrity monitoring by scanning your website hourly, twicedaily or daily. Any modification made to a file will be detected: file content, file permissions, file ownership, timestamp as well as file creation and deletion.
Watch your website traffic in real time
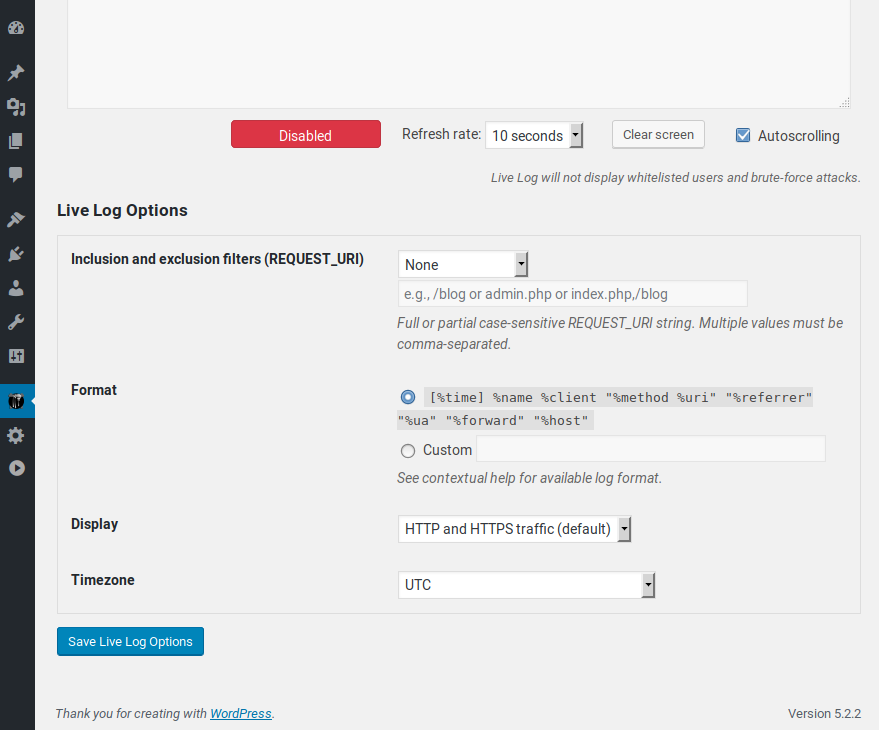
Live Log lets you watch your website traffic in real time. It displays connections in a format similar to the one used by the tail -f Unix command. Because it communicates directly with the firewall, i.e., without loading WordPress, Live Log is fast, lightweight and it will not affect your server load, even if you set its refresh rate to the lowest value.
Event Notifications
NinjaFirewall can alert you by email on specific events triggered within your blog. Some of those alerts are enabled by default and it is highly recommended to keep them enabled. It is not unusual for a hacker, after breaking into your WordPress admin console, to install or just to upload a backdoored plugin or theme in order to take full control of your website. NinjaFirewall can also attach a PHP backtrace to important notifications.
Monitored events:
- Administrator login.
- Modification of any administrator account in the database.
- Plugins upload, installation, (de)activation, update, deletion.
- Themes upload, installation, activation, deletion.
- WordPress update.
- Pending security update in your plugins and themes.
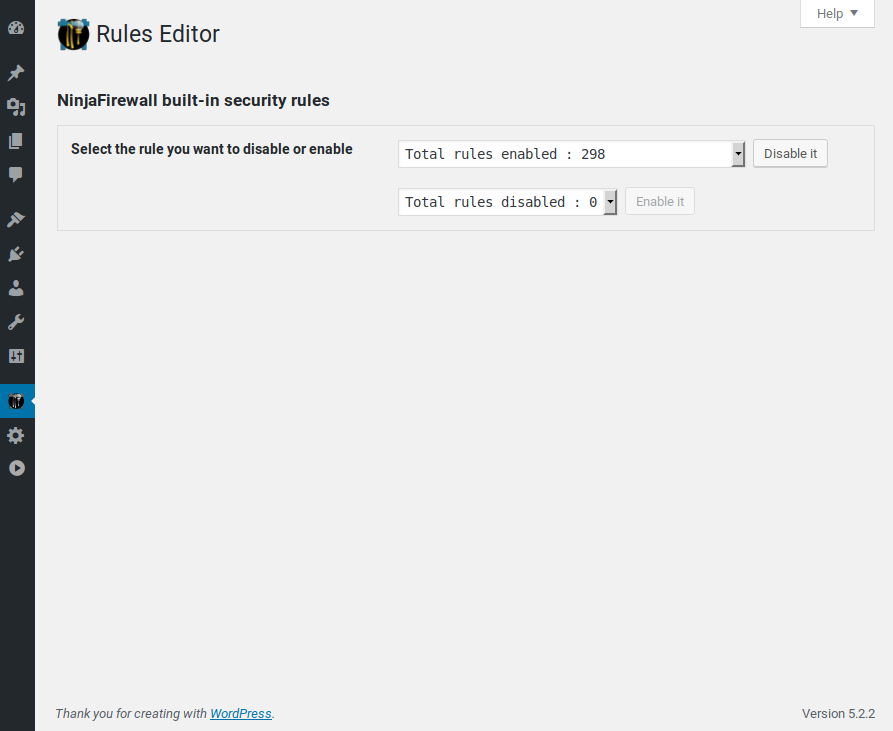
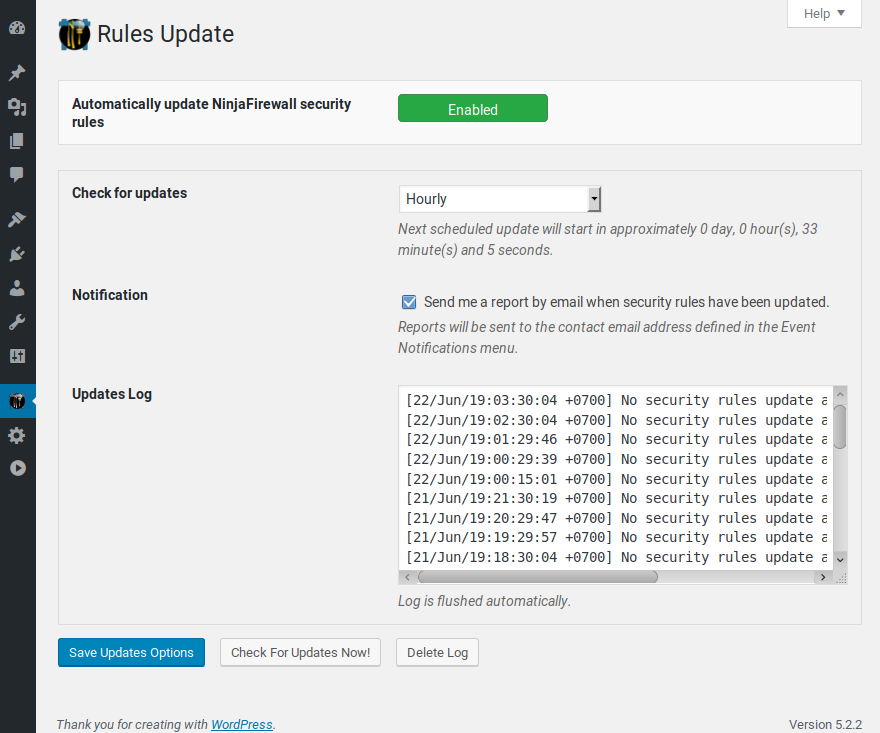
Stay protected against the latest WordPress security vulnerabilities
To get the most efficient protection, NinjaFirewall can automatically update its security rules daily, twice daily or even hourly. Each time a new vulnerability is found in WordPress or one of its plugins/themes, a new set of security rules will be made available to protect your blog immediately.
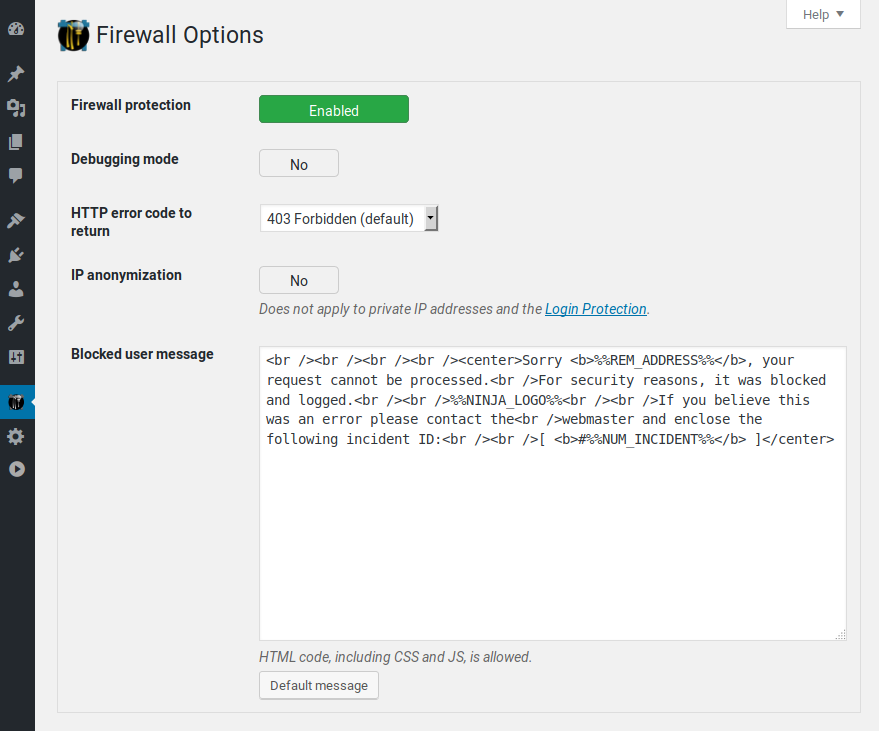
Strong Privacy
Unlike a Cloud Web Application Firewall, or Cloud WAF, NinjaFirewall works and filters the traffic on your own server and infrastructure. That means that your sensitive data (contact form messages, customers credit card number, login credentials etc) remains on your server and is not routed through a third-party company’s servers, which could pose unnecessary risks (e.g., decryption of your HTTPS traffic in order to inspect it, employees accessing your data or logs in plain text, theft of private information, man-in-the-middle attack etc).
Your website can run NinjaFirewall and be compliant with the General Data Protection Regulation (GDPR). See our blog for more details.
IPv6 compatibility
IPv6 compatibility is a mandatory feature for a security plugin: if it supports only IPv4, hackers can easily bypass the plugin by using an IPv6. NinjaFirewall natively supports IPv4 and IPv6 protocols, for both public and private addresses.
Multi-site support
NinjaFirewall is multi-site compatible. It will protect all sites from your network and its configuration interface will be accessible only to the Super Admin from the network main site.
Possibility to prepend your own PHP code to the firewall
You can prepend your own PHP code to the firewall with the help of an optional distributed configuration file. It will be processed before WordPress and all its plugins are loaded. This is a very powerful feature, and there is almost no limit to what you can do: add your own security rules, manipulate HTTP requests, variables etc.
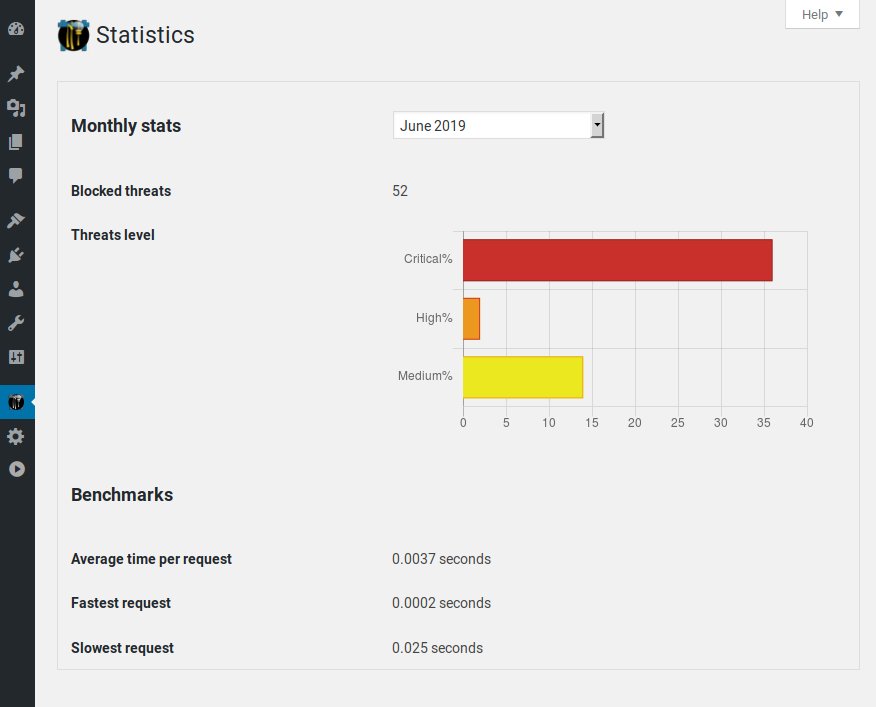
Low Footprint Firewall
NinjaFirewall is very fast, optimised, compact, and requires very low system resource.
See for yourself: download and install the Code Profiler plugin and compare NinjaFirewall’s performance with other security plugins.
Non-Intrusive User Interface
NinjaFirewall looks and feels like a built-in WordPress feature. It does not contain intrusive banners, warnings or flashy colors. It uses the WordPress simple and clean interface and is also smartphone-friendly.
Contextual Help
Each NinjaFirewall menu page has a contextual help screen with useful information about how to use and configure it.
If you need help, click on the Help menu tab located in the upper right corner of each page in your admin panel.
Need more security ?
Check out our new supercharged edition: NinjaFirewall WP+ Edition
- Unix shared memory use for inter-process communication and blazing fast performances.
- IP-based Access Control.
- Role-based Access Control.
- Country-based Access Control via geolocation.
- URL-based Access Control.
- Bot-based Access Control.
- Centralized Logging.
- Antispam for comment and user regisration forms.
- Rate limiting option to block aggressive bots, crawlers, web scrapers and HTTP attacks.
- Response body filter to scan the output of the HTML page right before it is sent to your visitors browser.
- Better File uploads management.
- Better logs management.
- Syslog logging.
Learn more about the WP+ Edition unique features. Compare the WP and WP+ Editions.
Requirements
- WordPress 4.7+
- Admin/Superadmin with
manage_options+unfiltered_html capabilities. - PHP 7.1+
- MySQL or MariaDB with MySQLi extension
- Apache / Nginx / LiteSpeed / Openlitespeed compatible
- Unix-like operating systems only (Linux, BSD etc). NinjaFirewall is NOT compatible with Microsoft Windows.
Screenshots
FAQ
ChangeLog