The easiest, most effective way to secure WordPress. Improve the security of any WordPress site in seconds.
Reduce your WordPress website’s risk to nearly zero with Solid Security
Formerly iThemes Security. Looking for iThemes? Learn more here.
On average, 30,000 websites are hacked every day.* Cyberattacks in the US increased by 57% in 2022.** Bad actors who want to hack your site, steal your data, and cripple your business are a 24/7/365 threat.
You need a proactive, strategic approach to WordPress website security that protects your site from brute force attacks, malware infections, and other cyber threats.
Solid Security shields your site from cyberattacks and prevents security vulnerabilities. It automatically locks out bad users identified by our Brute Force Protection Network that is nearly 1 million sites strong and leverages your own blacklist. It secures and protects your most commonly attacked part of your WordPress website – user login authentication.
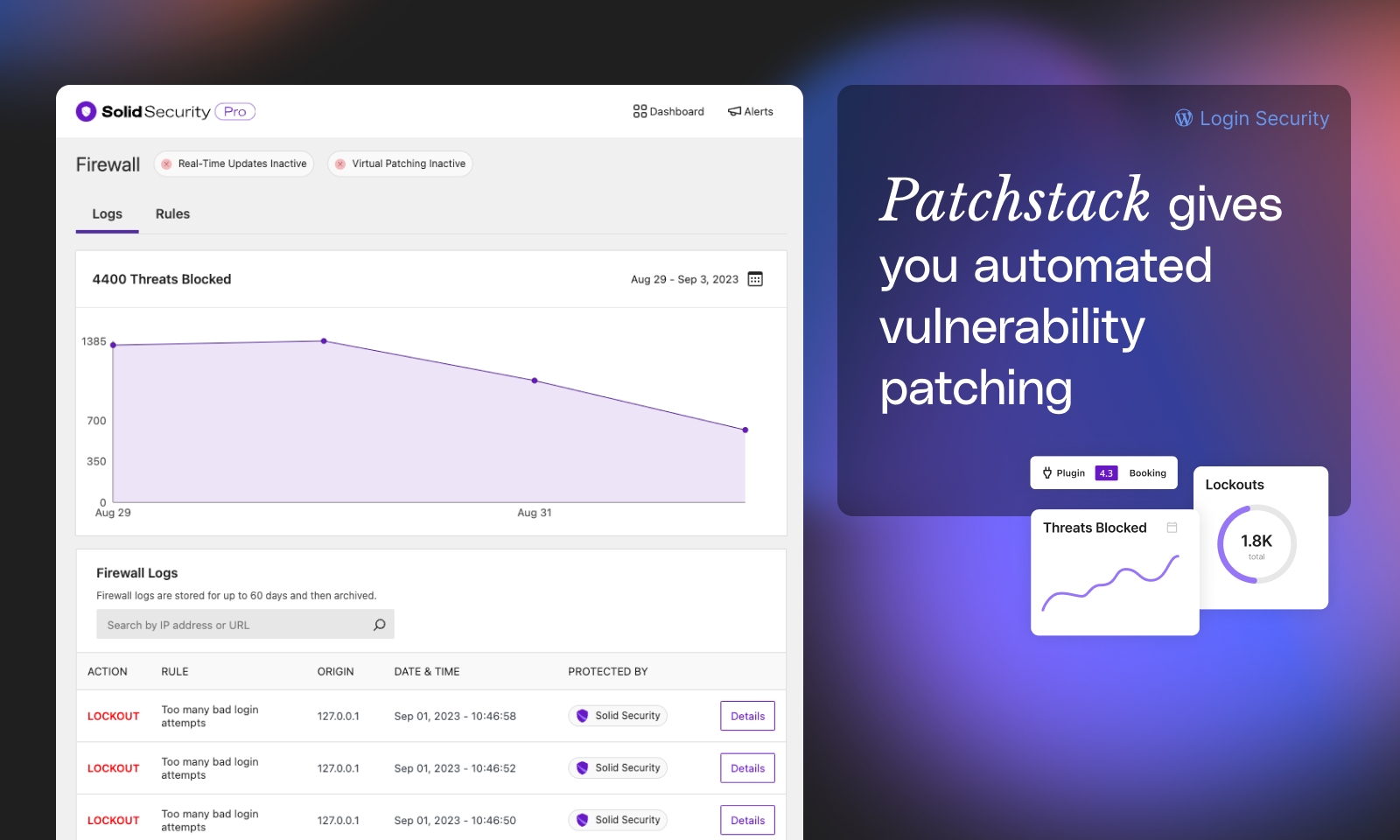
With Patchstack integration (Pro) protects your site before you even have a chance to address vulnerabilities and before a plugin or theme vendor or developer can even issue a patch.
That’s 24/7/365 always-on truly Solid Security.
???? Secure your Website in Minutes
The Solid Security setup and onboarding experience allows anyone to secure their WordPress website in under 10 minutes, regardless of technical acumen. Knowing that you have enabled all the right security settings for your website will leave you feeling like your site has never been more secure.
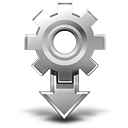
???? Security Site Templates to Fit Your Type of Site
Enabling the correct security settings based on the type of website you are building or maintaining is essential for proper security. An eCommerce site requires a different level of security than a basic blog. Solid Security Site Templates make it quick and easy to apply the right security settings for your website.
Choose from six different site templates to apply the type of security your site needs:
- Ecommerce – websites that sell products or services
- Network – websites that connect people or communities
- Non-Profit – websites that promote your cause and collect donations
- Blog – websites that share your thoughts or start a conversation
- Portfolio – websites that showcase your craft
- Brochure – simple websites that promote your business
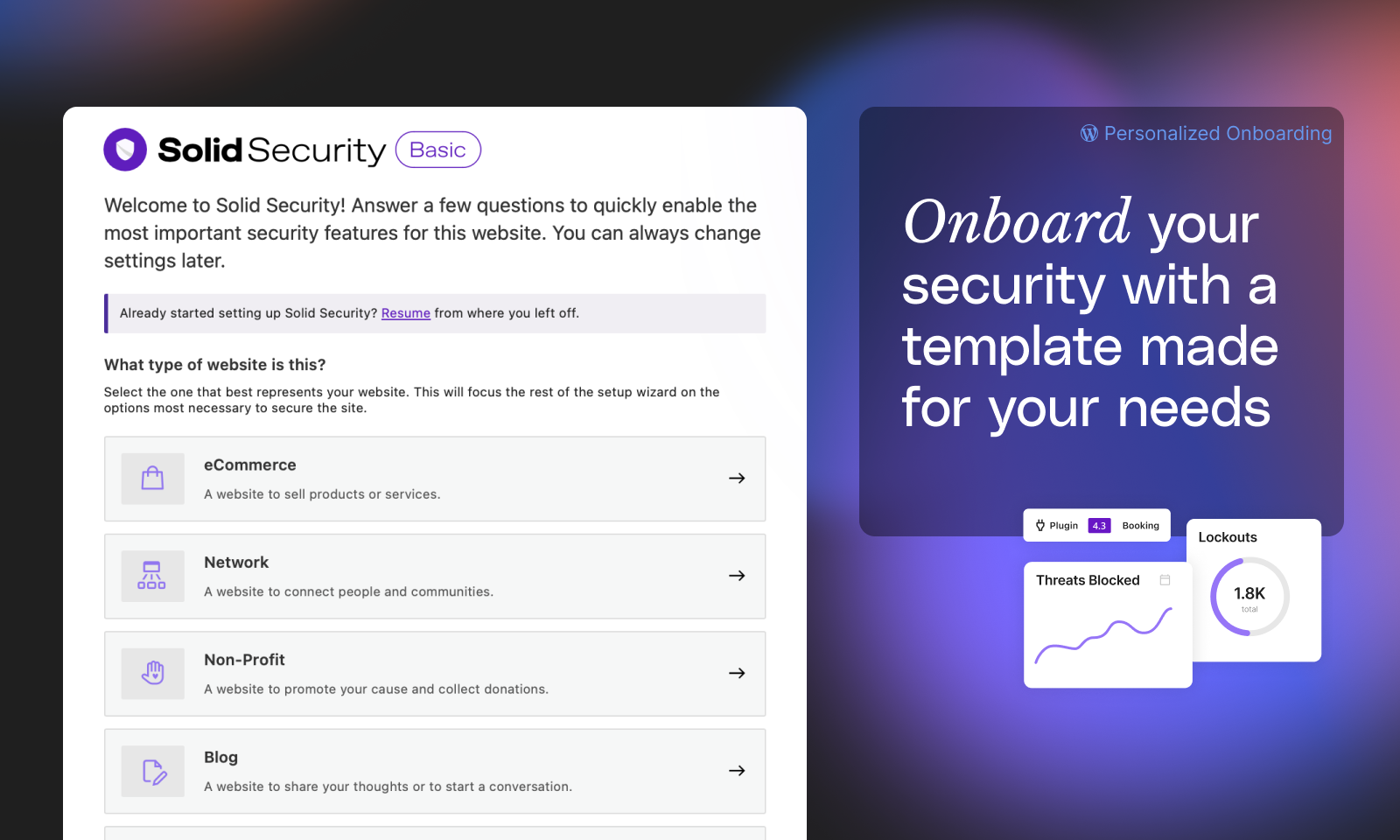
⌚ Real-Time Website Security Dashboard
Every day, lots of activity is happening on your website that you can’t see. Many of these activities can be related to your site’s security, so monitoring these events is vital to keeping your site secure.
The Solid Security Pro plugin provides a real-time WordPress security dashboard that monitors security-related events on your site around the clock. The Solid Security Dashboard is a dynamic dashboard with all your WordPress website’s security activity stats in one place, including brute force attacks, banned users, active lockouts, site scan results, and user security stats (Pro).
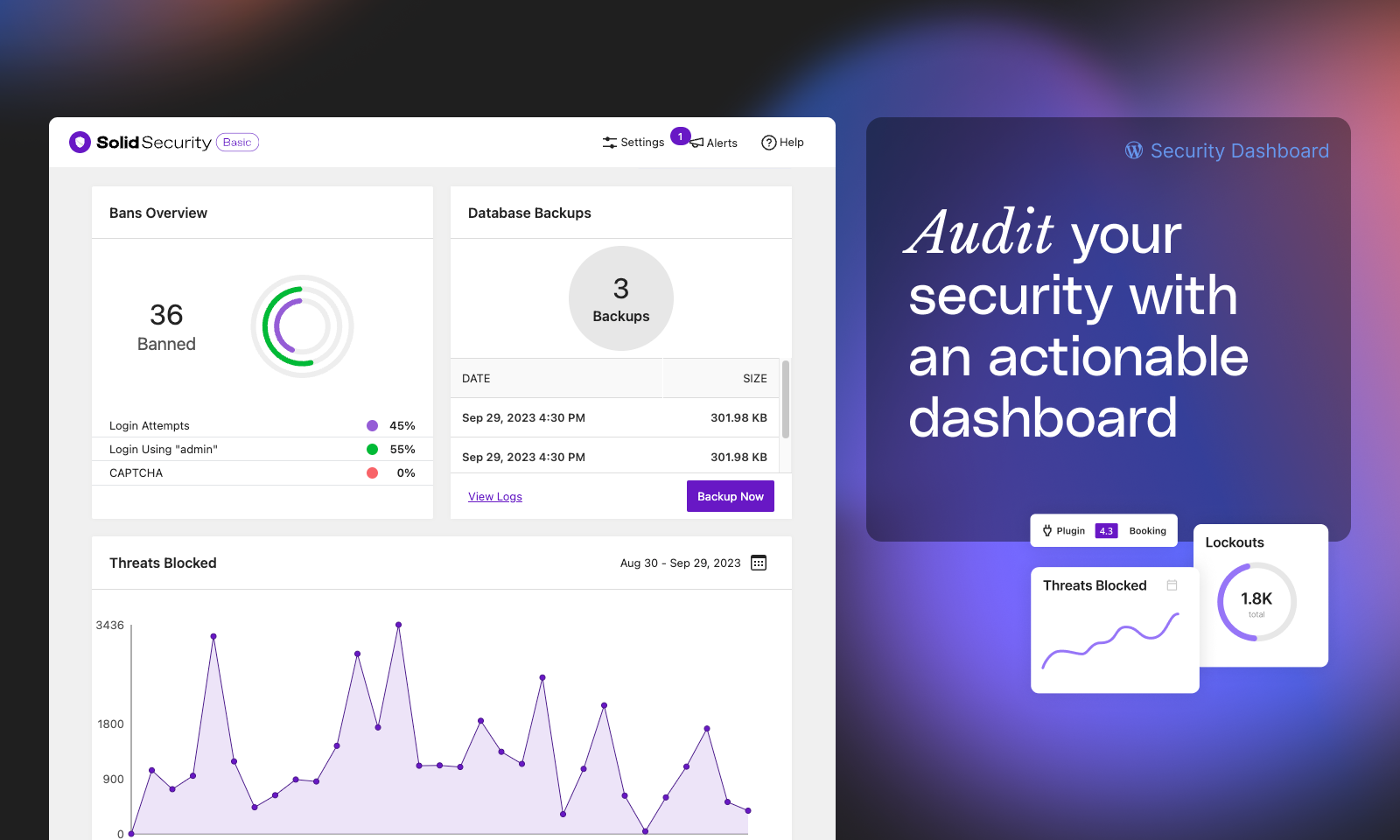
????️ WordPress Login Security
Setting up and maintaining proper WordPress configurations and managing user account access are essential aspects of hardening your site against threats and vulnerabilities. Basic and Pro include features that address both of these factors.
-
Two Factor Authentication (2FA) – Make your WordPress login nearly impenetrable to attack by requiring users to enter a security code along with a password to login. The Solid Security plugin allows you to add two-factor authentication to your WordPress login with several authentication methods, including mobile apps like Authy and Google Authenticator, email, and backup codes.
-
Password Requirements – Create and enforce a password policy for your users in less than a minute.
-
reCAPTCHA (Pro) – Stop bad bots from engaging in abusive activities on your website, such as attempting to break into your website using compromised passwords, posting spam, or even scraping your content.
-
Passwordless Logins (Pro) – WordPress security made easy. Secure your user accounts with 2fa & strong passwords while allowing real users login with a click of a mouse.
-
Trusted Devices (Pro) – Identify the devices you and other users use to block session hijacking attacks and limit Administrator privileges to Trusted Devices.
-
Automated Vulnerability Patching (Pro) – Solid Security Pro includes Patchstack which patches vulnerabilities before you have a chance to and applies fixes even before a plugin developer or vendor has issued a patch.
Learn more about how passwordless login is the future and how Solid Security can help you implement it today.
???????????????? The Right Amount of Security for Every User Level
Different types of user levels require different levels of security. During the Solid Security setup process, you can identify your website’s key user groups. Once the different types of users are identified, you can apply the level of security that is just right for each user group.
Here are a couple of examples of how User Groups are useful for securing your site:
-
For Clients – Let’s say you are configuring Solid Security on a client’s website. You will decide whether or not they are required to use two-factor authentication and if they should have access to the Solid Security settings.
-
For Customers – If you have an eCommerce website, you will decide whether or not you want to protect customer accounts with a password policy.
Privilege Escalation (Pro) also adds a safe, secure way to grant temporary admin-level access to your website.
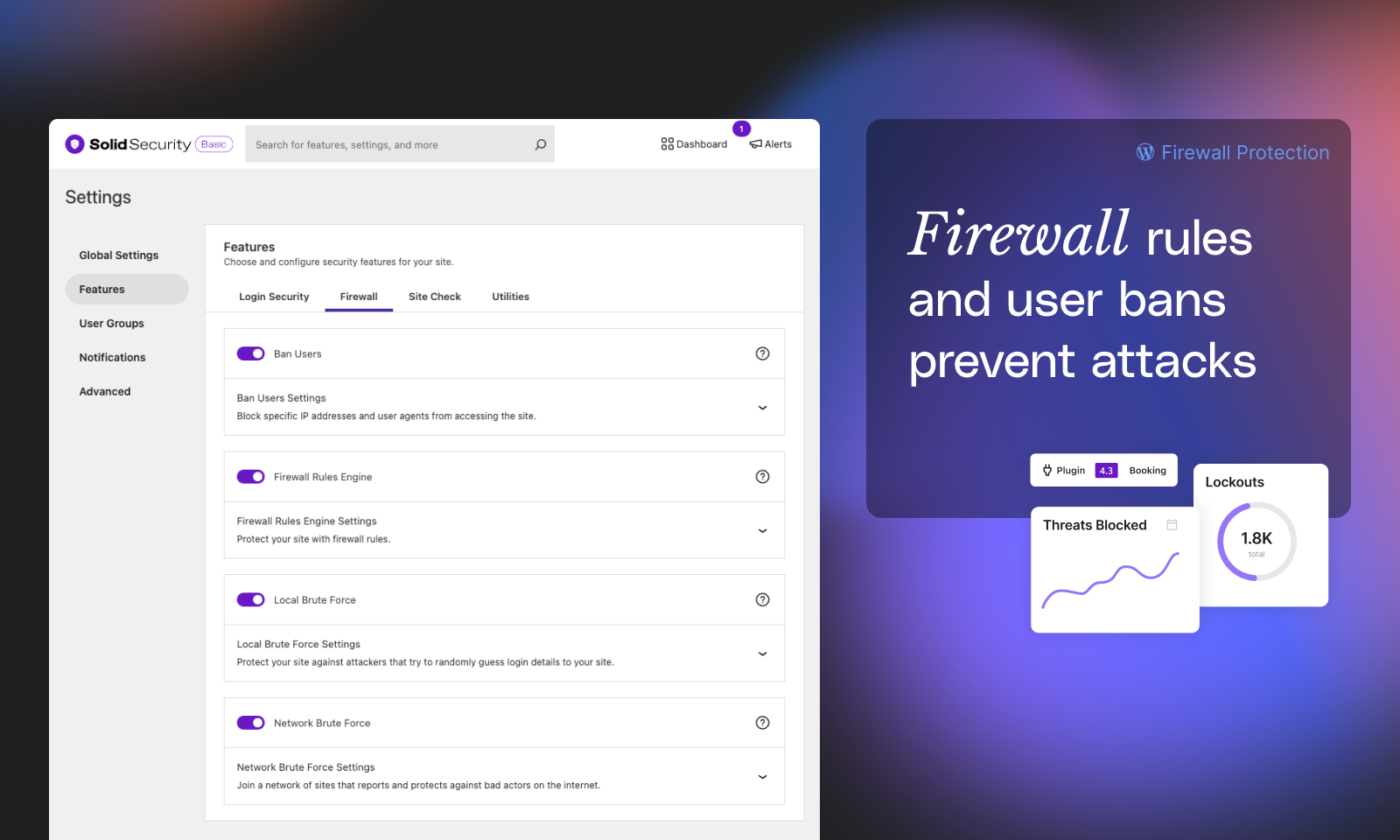
???? Block Bad Bots & Ban User Agents with Lockouts
-
Ban Users (Basic and Pro) – Permanently block repeat offenders from accessing your site.
Local Brute Force Protection – Automatically identify and stop the most common method of attack on WordPress sites.
-
Local Brute Force Protection (Basic and Pro) – Automatically identify and stop the most common method of attack on WordPress sites.
-
Network Brute Force Protection (Basic and Pro) – The network is the Solid Security community and is nearly one million websites strong. If someone tries to break into websites in the Solid Security community, Solid Security will block them across the network.
-
Magic Links (Pro) – Security shouldn’t get in your way. Magic Links allow you to log in to your WordPress site while your username is locked out by the Solid Security Local Brute Force Protection feature.
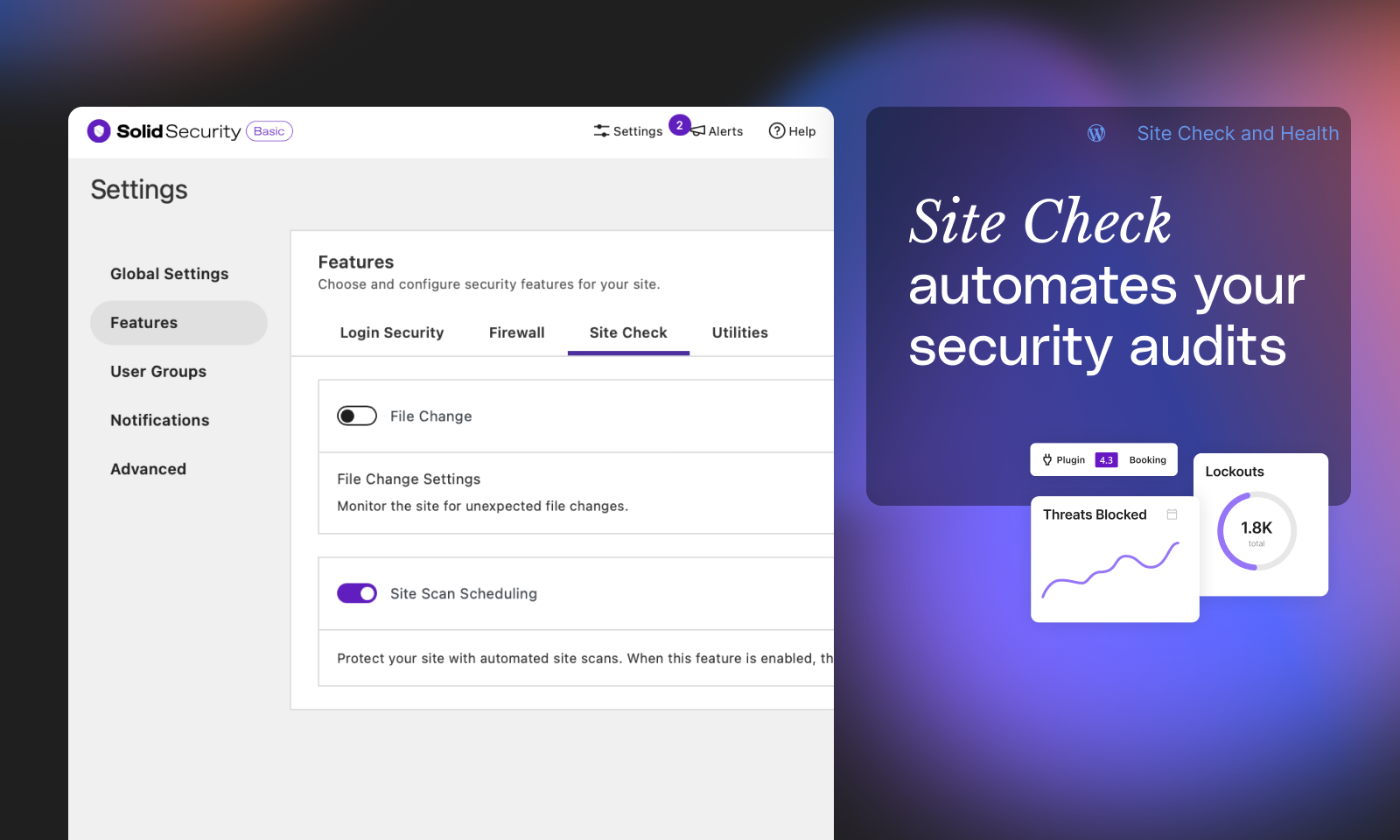
???? Monitor Your Site’s Security Health
-
File Change Detection (Basic and Pro) – Solid Security logs changes made to your website that can help detect malicious activity on your website.
-
Site Scanner (Basic and Pro) – Enable twice-daily checks for known vulnerabilities of WordPress core file, plugins and themes. Using the Google Safe Browsing API, the Site Scan also checks your Google’s blocklist status and will alert you if Google has found any malware on your website.
-
Site Scanner (Pro) – Unlock Version Management to automatically apply a patch to vulnerable software detected by the Site Scan when one is available.
-
User Logging (Pro) – Keep a record of user activity in your WordPress security logs, including login/logout, user registration, adding/removing plugins, switching themes, changes to posts and pages, and more.
-
Version Management (Pro) – The Version Management feature in Solid Security Pro allows you to auto-update WordPress, plugins, and themes. Beyond that, Version Management also has options to harden your website when you are running outdated software and scan for old websites.
????️ Website Security Utilities
-
Enforce SSL – Force all connections to the website to be made over SSL/TLS.
-
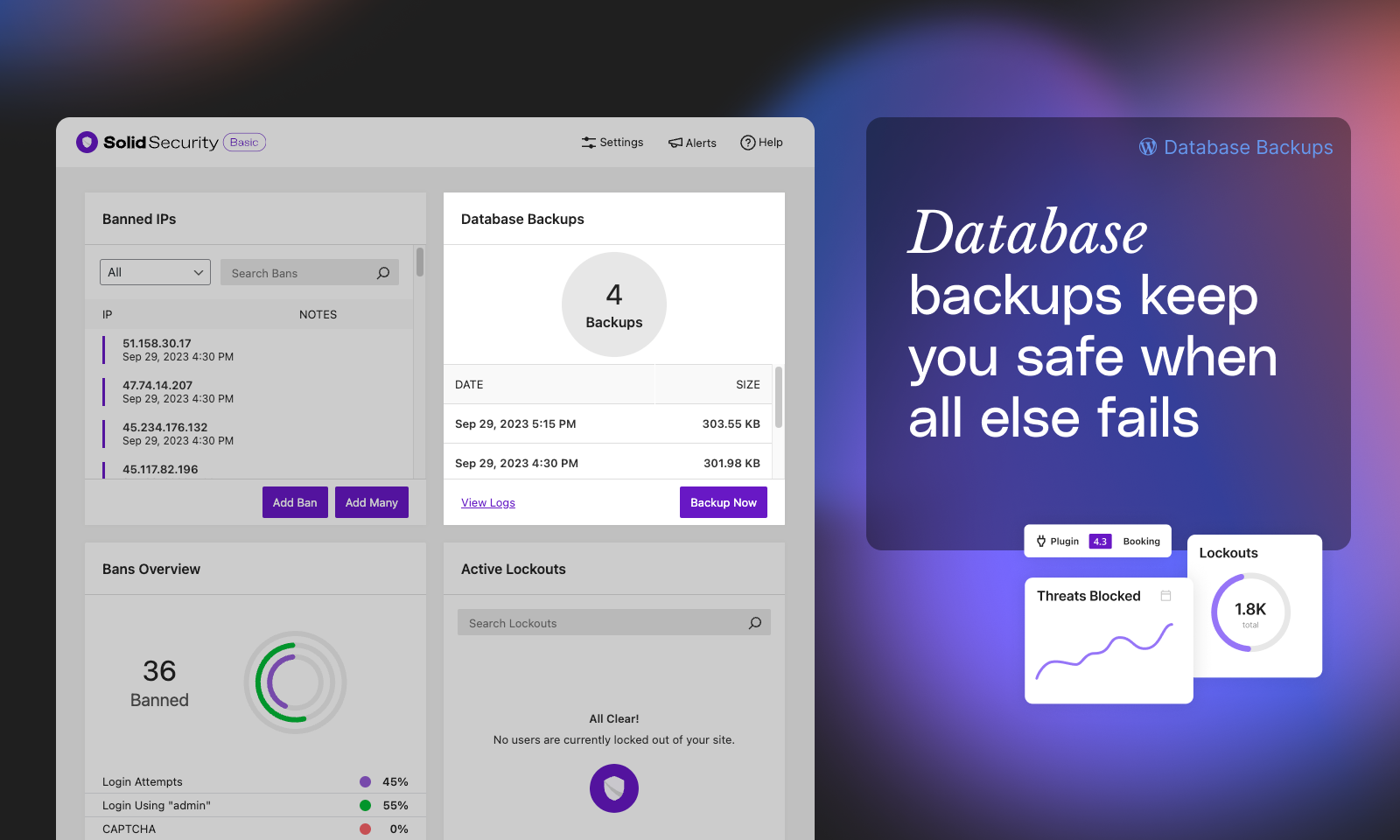
Database Backups – Create backups of your WordPress database. (Not a complete backup.)
-
Geolocation (Pro) – Improve Trusted Devices by connecting to an external location or mapping API.
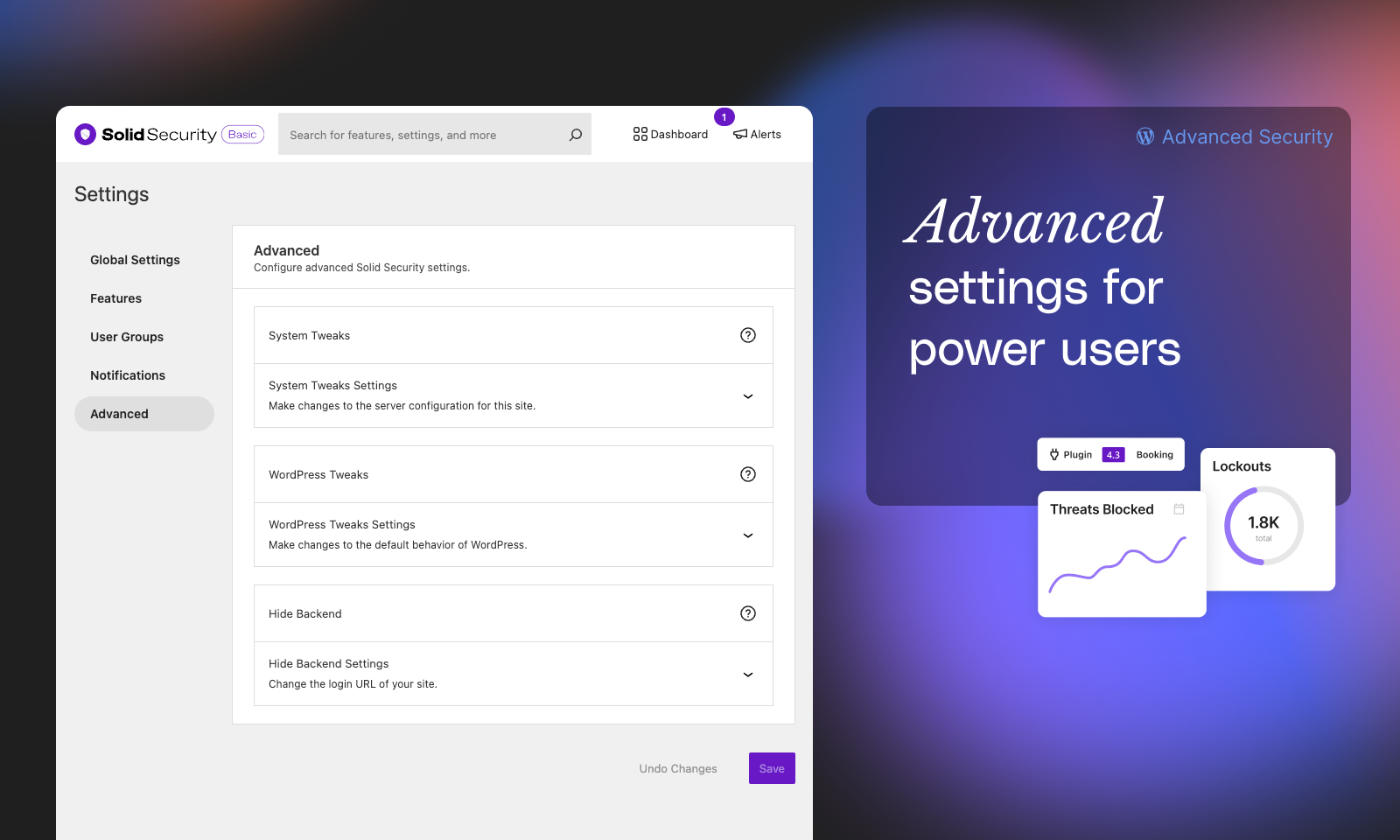
???? Advanced Security Tools
- Identify Server IPs – Prevent issues caused by inadvertently locking out your server IPs.
- Change User ID 1 – Change the user ID for the first WordPress user, potentially preventing attacks that assume the user with ID1 exists and is an administrator.
- Change Database Prefix – Change the database prefix that WordPress uses, potentially preventing attacks that assume the database prefix is “wp_”.
- Check File Permission – See the file and directory permissions of key areas of your site.
- Server Config Rules – View or flush the server security rules generated by Solid Security.
- wp-config.php Rules – View or flush the wp-config.php security rules generated by Solid Security.
- Change WordPress Salts – Secure your site after a successful attack by changing the WordPress salts used to secure cookies and security tokens.
- Hide Login URL – change the login URL of your site, making it harder for bots to find your login page and attack it.
???? Need Help?
Free support may be available with the community’s help in the WordPress.org support forums. Our Solid Security support team provides top-notch technical support to all our Solid Security Basic users there.
Our Help Center will help you become an iThemes Security expert.
Get additional peace of mind with professional support from our expert team and pro features to take your site’s security to the next level with Solid Security Pro.
Recover From a Hacked Site
Solid Security makes regular backups of your WordPress database, allowing you to get back online quickly in the event of a hack or security breach. Use Solid Security to create and email database backups on a customizable schedule.
For complete site backups and the ability to restore or move WordPress to a new host or domain, check out Solid Backups.
Solid Central Integration
Manage more than one WordPress site? Release lockouts and keep your themes, plugins, and WordPress core up to date from one dashboard with Solid Central.
*Zippia. “30 Crucial Cybersecurity Statistics [2023]: Data, Trends And More” Zippia.com. Jun. 15, 2023, https://www.zippia.com/advice/cybersecurity-statistics/
**https://blog.checkpoint.com/2023/01/05/38-increase-in-2022-global-cyberattacks/
License
Released under the terms of the GNU General Public License.
Screenshots
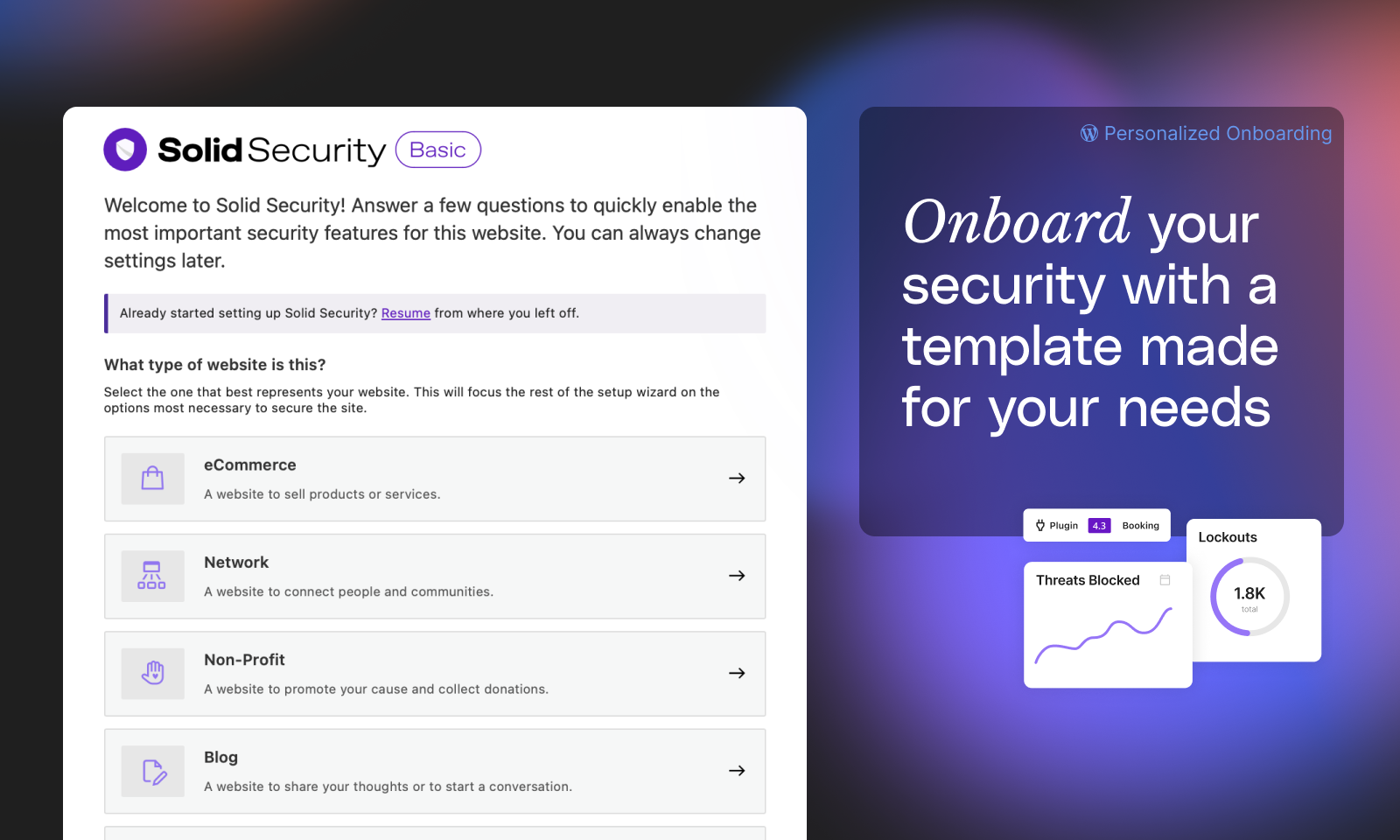
Customized onboarding configures your security settings to your needs
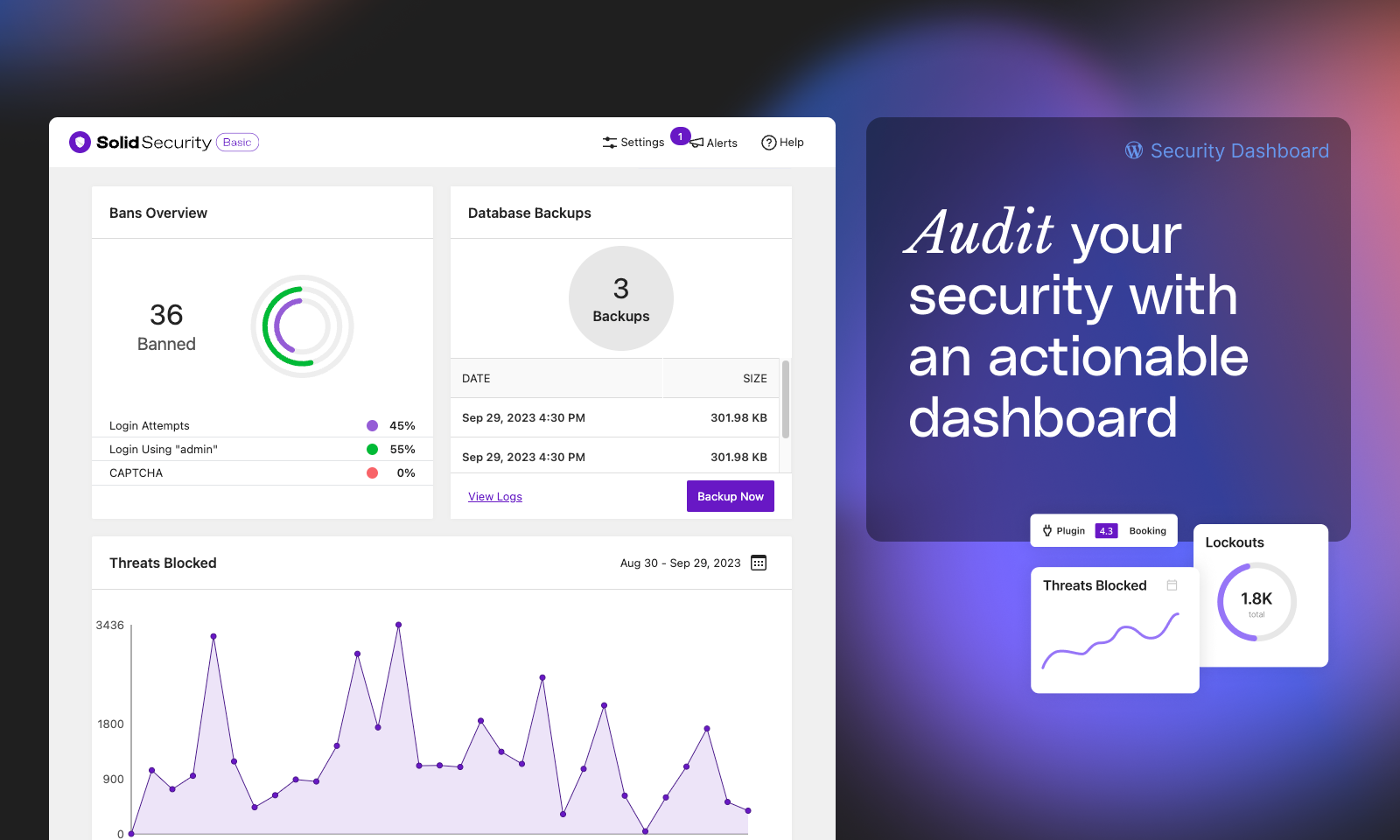
Real-Time Security Dashboard
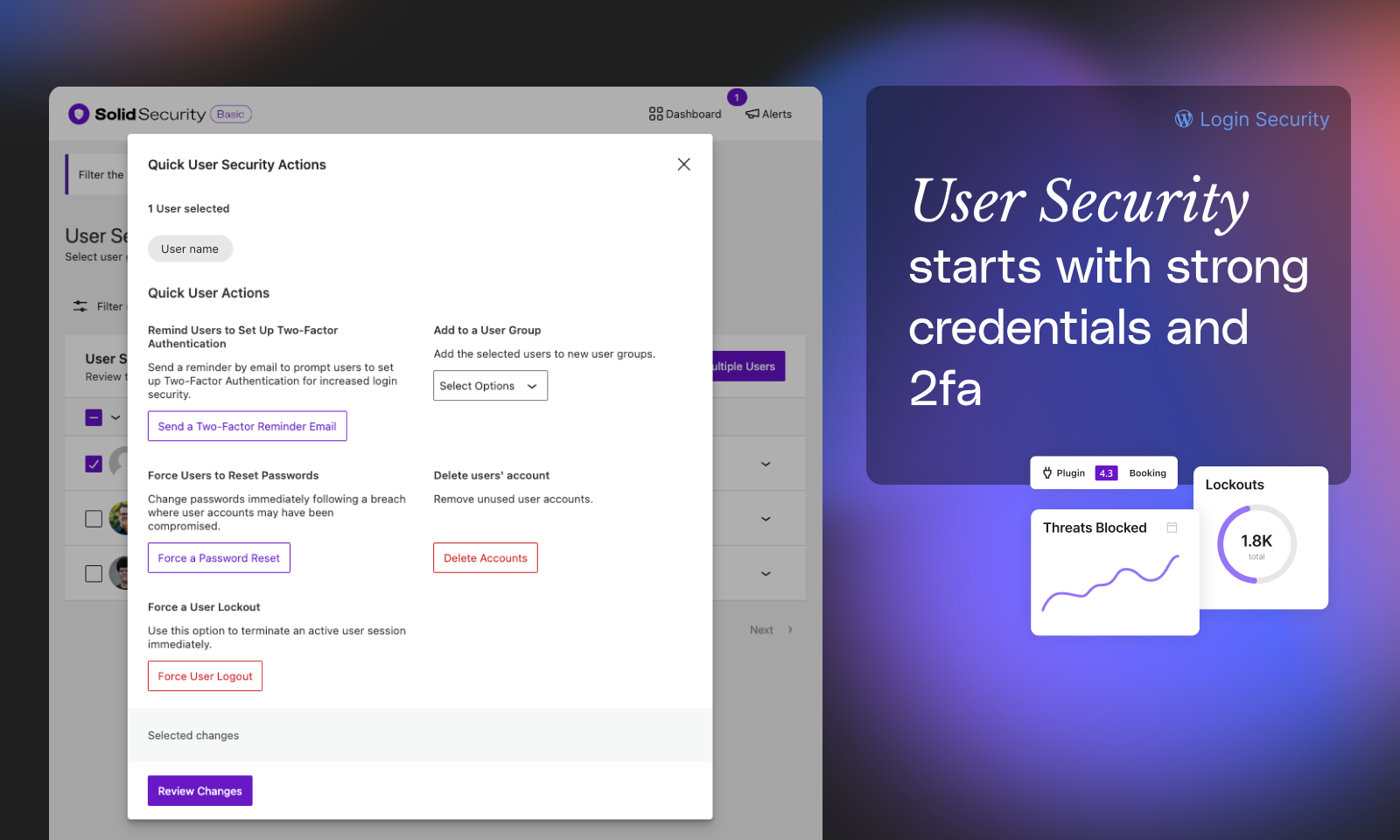
WordPress Login Security with Two Factor Authentication
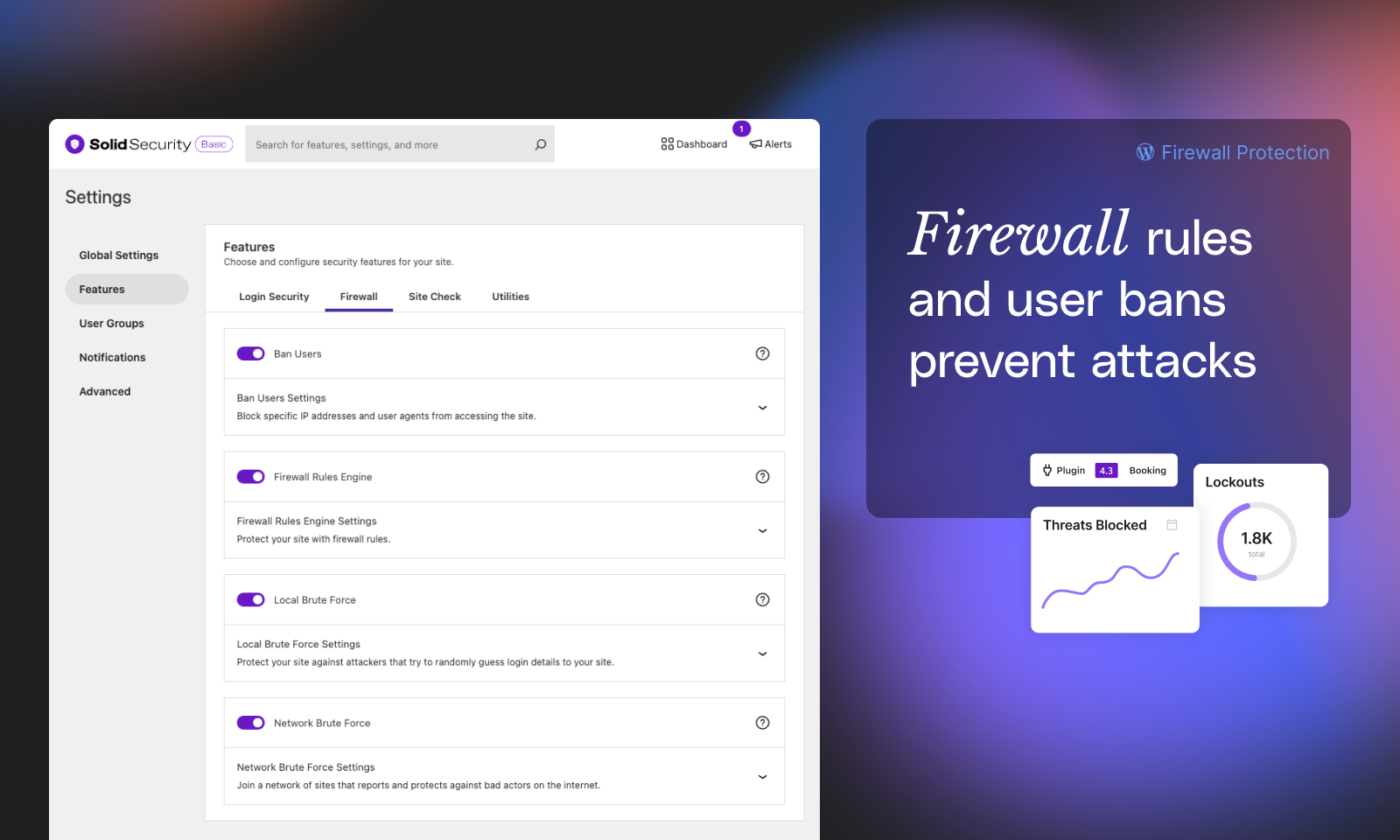
Firewall rules, Block Bad Bots, and Ban User Agents with Lockouts
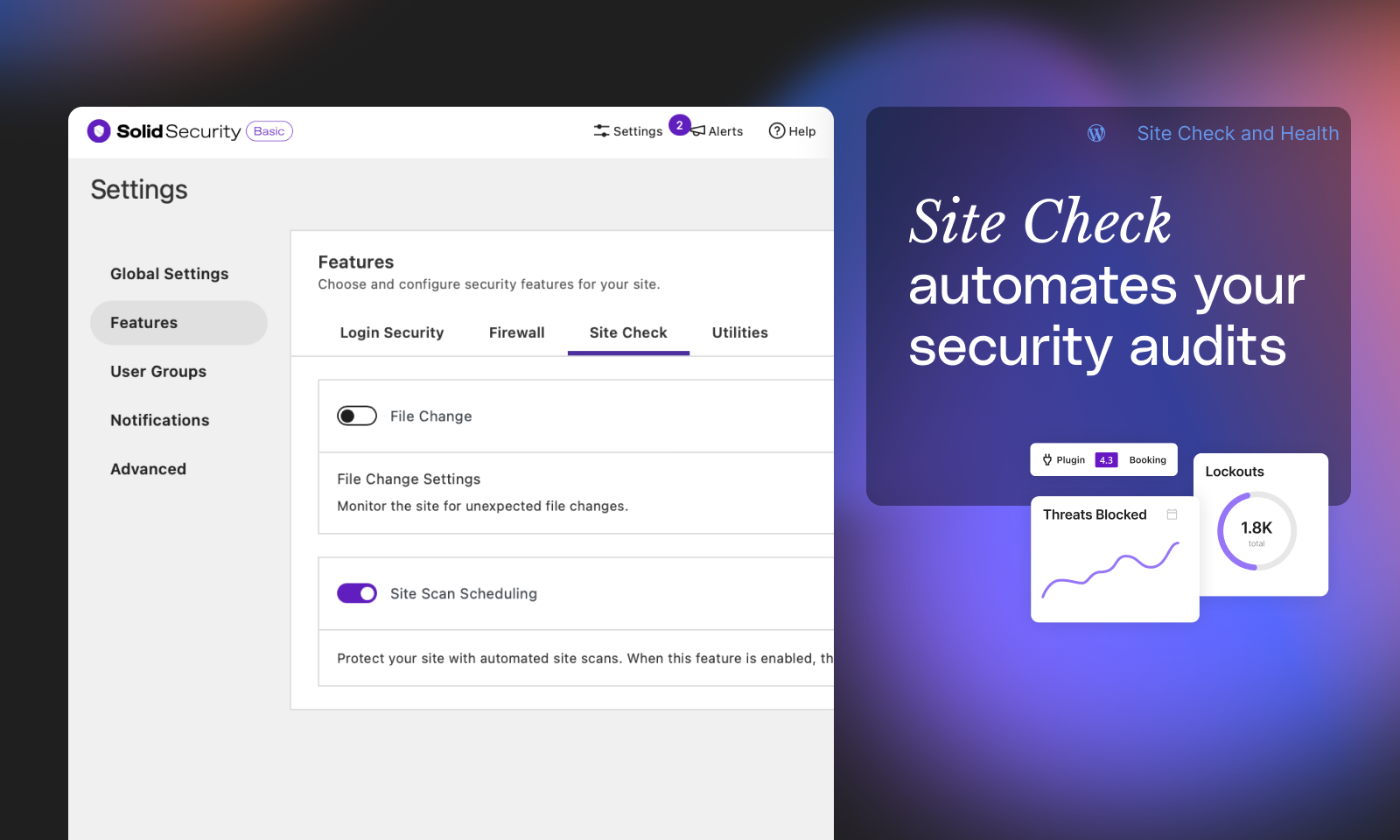
Monitor Your Site's Security Health
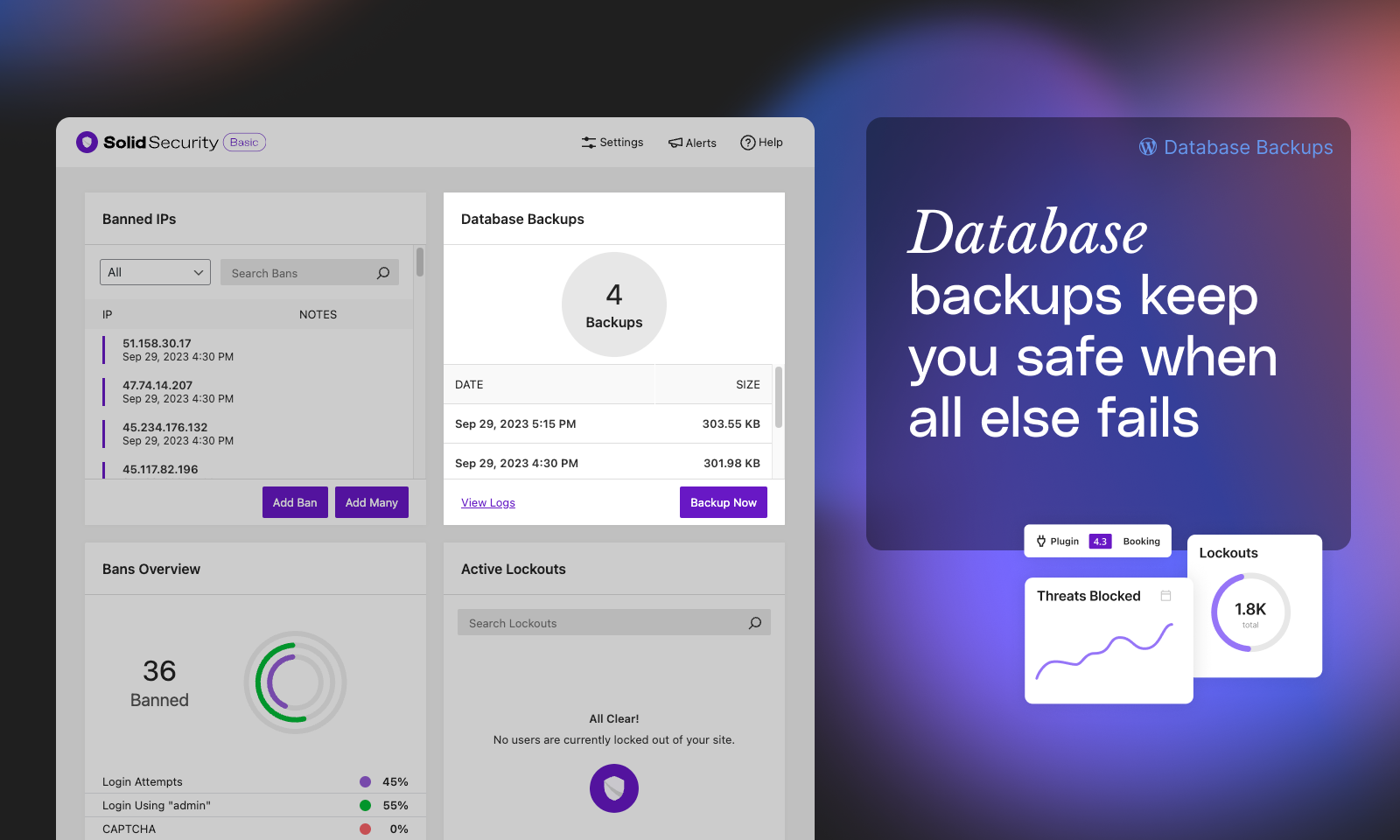
Database backups help you get up and running again when the worst happens
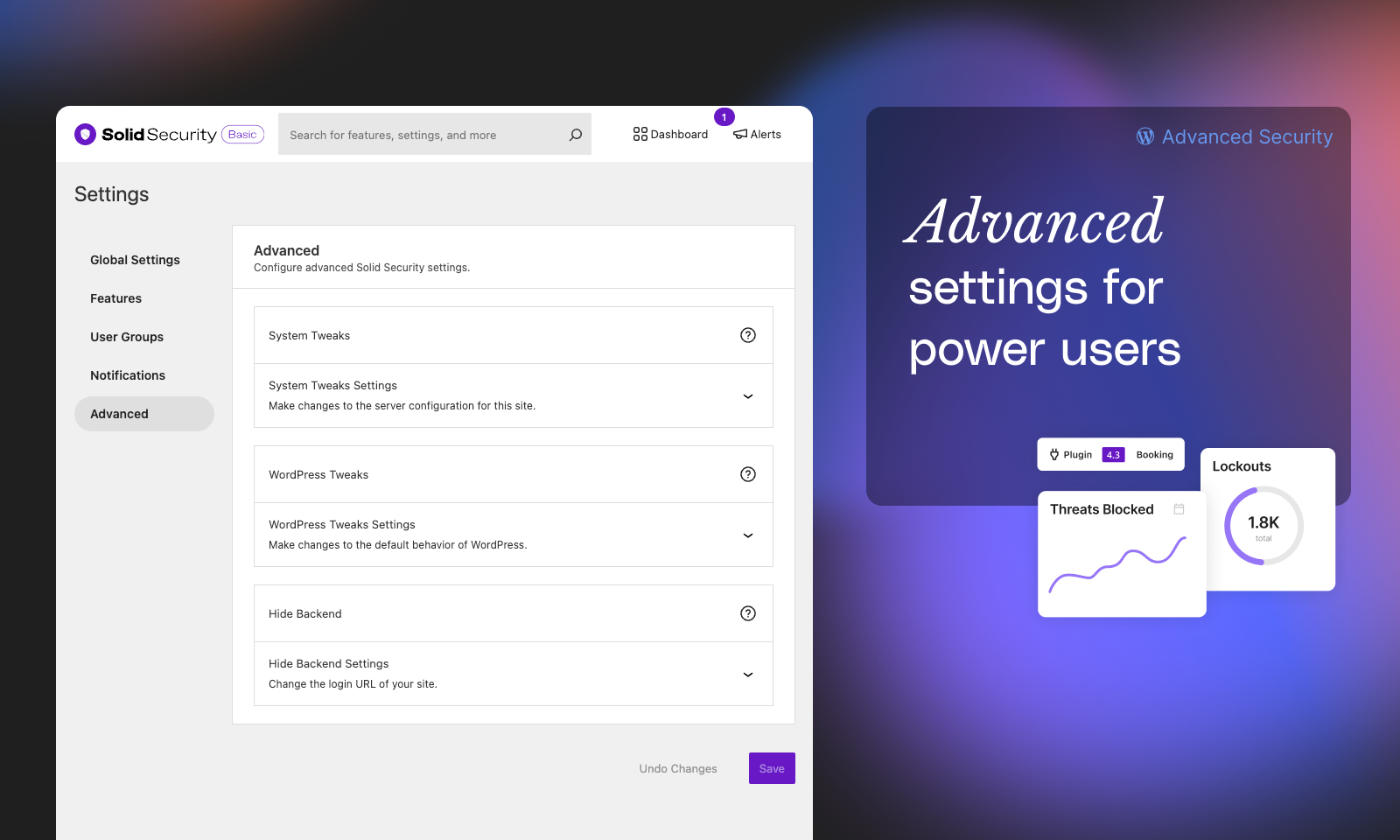
Advanced Security Settings for power users
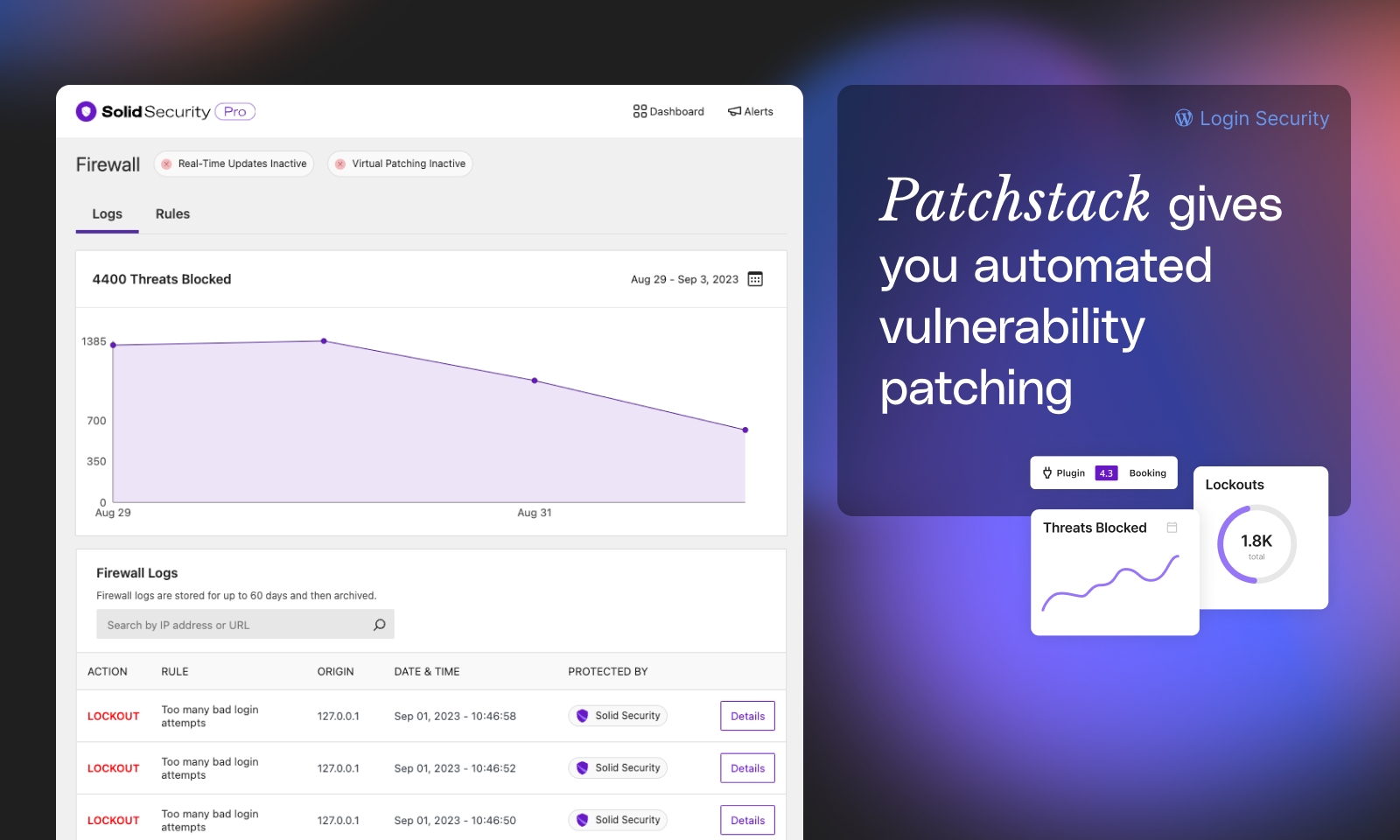
Automated vulnerability patching with Patchstack (Pro)
Why does Solid Security require the latest WordPress version? Can’t I use a slightly older version?
- One of the best security practices for a WordPress site owner is keeping software up to date. Because of this, we only test this plugin on the latest stable version of WordPress and will only guarantee it works in the latest version.
Will this plugin completely stop all attacks on my site?
- No. Solid Security is designed to help improve the security of your WordPress installation from many common attack methods, but it cannot prevent every possible attack. Nothing replaces diligence and good practice. This plugin makes it a little easier for you to apply both.
Is this plugin only for new WordPress installs or can I use it on existing sites, too?
- While Solid Security can be installed on either a new or existing site, we strongly recommend making a complete backup of your existing site before applying any features included in this plugin.
Will this plugin work on all servers and hosts?
- Solid Security requires Apache or LiteSpeed and mod_rewrite or NGINX to work.
What changes does this plugin make that can break my site?
- Solid Security makes significant changes to your database and other site files which can be problematic for existing WordPress sites. Again, we strongly recommended making a complete backup of your site before using this plugin. While problems are rare, most support requests involve the failure to make a proper backup before installation. DISCLAIMER: Under no circumstances do we release this plugin with any warranty, implied or otherwise. We cannot be held responsible for any damage that might arise from the use of this plugin.
ChangeLog
9.3.2
- Important: “Automatic (Insecure)” IP detection has been removed. Read more: https://go.solidwp.com/firewall-features-not-available
- Enhancement: Allow generating a new Two-Factor TOTP secret from the WP-Login UI.
- Bug Fix: The SolidWP logo appeared too large in some email clients.
- Bug Fix: An error would occur if we could not determine the length of database columns while saving log items.
9.3.1
- Tweak: Add a notice when a user’s role is demoted from the Site Scans page.
- Tweak: Update Privacy Policy generator text.
- Bug Fix: Could not proceed through onboarding when BuddyPress or BuddyBoss was active.
- Bug Fix: Some firewall rules could not be deactivated.
- Bug Fix: Allow opting in to Telemetry via the Settings Page.
- Bug Fix: PHP 8.2 deprecation warnings.
9.3.0
- New: The Firewall page has a new IP Management tab to provide easy access to blocking or authorizing IP addresses.
- New: Usage Data Sharing (opt-in only) allows users to share non-personal and non-sensitive information with StellarWP to inform decisions about how to improve Solid Security in the future.
- Enhancement: Add a snackbar notice when making changes on the Firewall Configure page.
- Tweak: Remove some straggling references and links to iThemes.
- Tweak: Consistently refer to 2FA as Two-Factor Authentication on the Profile page.
- Tweak: Allow performing more Site Scan actions when the issue is muted.
- Bug Fix: Truncate log item columns that are too long before inserting into the database.
- Bug Fix: Consistently order the Security Profile tabs.
- Bug Fix: Add missing text domain to new Solid Security Admin Menu items.
- Bug Fix: Reset filters on the Vulnerabilities page when starting a Site Scan.
- Bug Fix: PHP warning on the logs page when the File Change module logs unexpected data.
9.2.0
- New: Refreshed UI for manging per-user security settings like Two-Factor. The previous Two-Factor UI can be enabled using the SOLID_SECURITY_LEGACY_2FA_UI constant.
- New: A new block “Solid Security User Security Settings” let’s you display this UI on the front-end of your website. The [solid_security_user_profile_settings] shortcode can be used if you’re not yet using the Block Editor.
- Important: Solid Security now requires WordPress 6.3 or later.
- Enhancement: Display a snackbar notice when sending a 2FA reminder from the Site Scan page.
- Enhancement: Include a link directly to the Patchstack database in the Site Scanner alert email.
- Tweak: Remove iThemes Security is now Solid Security banners from the admin.
- Bug Fix: Trying to enable Network Brute Force from the Security messages center linked to the wrong place.
- Bug Fix: During onboarding, a double scrollbar was displayed on some screen sizes.
9.1.0
- New: Add support for creating custom firewall rules.
- Enhancement: Add support for configuring firewall settings from the Firewall page.
- Bug Fix: The firewall page would appear empty when geolocation could not retrieve a country code.
9.0.3
- Bug Fix: Remove an extra folder containing duplicate plugin files
9.0.2
- Bug Fix: Adding missing dist files to SVN
9.0.1
- Security: Don’t disclose the login URL when using Hide Backend on a site with comments enabled and comment registration required. Thanks to Naveen Muthusamy for disclosing this issue.
- Hardening: Check for the promote_user capability when using Privilege Escalation in addition to edit_user.
- Tweak: Remove the iThemes Security is now Solid Security banner from admin-facing email notifications.
- Bug Fix: Prevent the User Security page from crashing when “Show Avatars” is disabled in the WordPress discussion settings.
- Bug Fix: Fix some filters on the User Security page not working as expected.
- Bug Fix: Fix spacing on the Two-Factor form when backup methods are enabled.
- Bug Fix: Fix fatal error when there is an error retrieving Patchstack license information.
- Bug Fix: Styling issues on WordPress 6.4.
9.0.0
- New: iThemes Security is now Solid Security! Learn More: https://go.solidwp.com/security-welcome-to-solidwp
- Important: Solid Security now requires WordPress 6.2 or later.
- New: The Firewall screen brings together the Firewall functionality Solid Security provides into one easy to use screen. More Firewall features are coming soon!
- New: The Vulnerabilities screen identifies what vulnerable software you have on your site and guides you through next steps.
- New: Identify risks in your site’s security with the the expanded Site Scan functionality.
- New: The User Security screen keeps you appraised of the security practices your site’s users are following. Easily apply actions to multiple users in one-click like resetting passwords or logging out active sessions.
- Enhancement: The dashboard and settings screens have been redesigned to make it easier to find what you’re looking for.
- Enhancement: The Security Summary dashboard card gives you a snapshot of the most important security issues affecting your site.
- Enhancement: Add support for loading Solid Security via an MU-Plugin for improved performance when blocking attackers.
- Tweak: Remove the IP Tracker Online link from the logs page.
- Bug Fix: PHP 8.2 compatibility.
- Bug Fix: Resolved PHP warnings when unexpected data is encountered during software updates.
8.1.8
- News: iThemes Security is becoming Solid Security soon. Learn More: https://go.solidwp.com/security-free-notice-ithemes-becoming-solidwp
8.1.7
- Important: Enforce encryption for Two-Factor secrets.
- Tweak: Add Stellar and Solid banners.
- Bug Fix: Don’t require “Write to Files” to be enabled to use the “Rotate Encryption Key” tool.
8.1.6
- Bug Fix: Fallback to the homepage when Enforce SSL encounters a non-safelisted redirect destination.
- Bug Fix: IP Detection on sites behind Load Balancers that appended their IP address to X-Forwarded-For and did not provide a Real IP header.
8.1.5
- Security Hardening: Prevent open redirects attacks against the Enforce SSL module. This attack requires spoofing the Host header which requires additional conditions to exploit. Thanks to nlpro for reporting the issue. Read More: https://ithemes.com/?p=84309
- Bug Fix: Update Password Strength library to the latest version. This fixes discrepancies between the realtime password strength estimation and the enforced password strength.
8.1.4
- Tweak: Add “All” tab to the Features page.
- Tweak: Don’t show “Ban” buttons in Security Dashboard if the user won’t be able to create a ban.
- Bug Fix: Prevent Headers Already Sent warning when a lockout occurs during a WP Cron request on some server setups.
- Bug Fix: Manually load Sodium Polyfill for servers that have an older version of libsodium installed.
- Bug Fix: Error when saving the File Change settings when the “notify_admin” setting was set.
- Bug Fix: Prevent a redirect loop when logging in on sites that take more than 5 seconds to load the Dashboard.
8.1.3
- Important: iThemes Security now requires PHP 7.3 and WordPress 5.9 or later.
- Security: Add support for encrypting Two-Factor Mobile App secrets. Enable via Tools -> Set Encryption Key.
- Security: Deprecate Automatic Proxy Detection. Instead, manually configure Proxy Detection or use Security Check. Fix IP spoofing attacks.
- Enhancement: Add “Ban Lockout” button to the Active Lockouts card.
- Bug Fix: File Logs not rotating.
- Bug Fix: PHP warning when loading Icon Fonts in certain configurations.
- Bug Fix: Don’t attempt to Hide Backend when a Cron request is being processed.
- Bug Fix: Prevent entering invalid date values when selecting a custom date range in the Security Dashboard.
- Bug Fix: Preliminary PHP 8.1 compatibility.
- Bug Fix: File Change “notify_admin” settings validation error.
- Thanks to Calvin Alkan for reporting the security issues fixed in this release.
8.1.2
- Tweak: Require a Title when creating a new Dashboard.
- Bug Fix: Don’t attempt to send a Site Scan notification for Clean scans preventing a fatal error after scheduled site scans.
8.1.1
- Bug Fix: Error when visiting the Notifications page after activating a module with notifications for the first time.
- Bug Fix: Update deprecated withState usages to useState.
8.1.0
- Important: iThemes Security now requires WordPress 5.8 or later.
- New Feature: Include the full iThemes Security Site Scanner in iThemes Security Free. Scheduled scans are disabled by default.
- Tweak: Add new “Go Pro” page that includes an overview of features in iThemes Security Pro.
- Bug Fix: Scroll to top of window when navigating.
- Bug Fix: Allow searching for Password Requirements.
- Bug Fix: Don’t load WordPress and System Tweaks modules when the
ITSEC_DISABLE_MODULES constant is enabled.
- Bug Fix: Prevent incidentally loading the Two-Factor module when it is unregistered.
- Bug Fix: Conditionally display the NGINX File Path setting.
- Bug Fix: Allow saving Notifications when “default recipients must contain at least 1 item” error is present.
- Bug Fix: Help styling on WordPress 5.9.
- Bug Fix: Compatibility with plugins that expected a logged-in user during lockouts.
8.0.2
- Enhancement: Reintroduce Feature Flags management UI.
- Tweak: Reposition “Advanced” and “Tools” menu items to be more readable on lengthy screens.
- Bug Fix: When the Change Admin User tool is run, update any User Groups referencing the old user id.
- Bug Fix: WordPress footer would appear in the middle of the logs page.
- Bug Fix: Add missing translation strings file.
8.0.1
- Bug Fix: Sites that did not support HTTPS, but had the SSL module active, but not configured, on upgrade would get redirected to the HTTPS version of the site.
- Bug Fix: Unregister the iThemes Security Two-Factor module when the Two-Factor Feature Plugin is enabled.
- Bug Fix: Allow activation on WordPress 5.7.0.
- Bug Fix: Add missing textdomains.
8.0.0
- Important: iThemes Security now requires WordPress 5.7 and PHP 7.0 or later.
- New: iThemes Security gets a redesigned interface focused on making it easier to configure and find what you’re looking for. Read More: https://ithemes.com/?p=65086.
- New: Instantly search over everything in iThemes Security with a new instant search feature.
- New: Security Tools have been grouped into their own page. “Identify Server IPs” and “Security Check Pro” can be run manually without using Debug Mode.
- New: Relevant content from the Help Center, iThemes Blog, and iThemes YouTube channel is surfaced in a new Help area based on the current page. Click the “Help” button in the toolbar or the “Info” icon next to the page title to access it.
- New: The settings UI is now fully responsive and works great across mobile, tablet, and desktop devices.
- New: Two-Factor is now part of the core iThemes Security plugin.
- Enhancement: Improved keyboard and screen reader support.
- Enhancement: The Banned Users Card can add multiple bans at once.
- Tweak: Add a new Global setting to control “Automatically Temporarily Authorize Hosts”.
- Tweak: When the Global setting “Hide Security Menu in Admin Bar” is enabled, notices will no longer be printed on non-iThemes Security pages. Instead, you can access the Message Center from the Settings or Dashbaord toolbars.
- Tweak: The Database Backups module is no longer available if you have BackupBuddy installed. If this behavior isn’t desired, enable the “ITSEC_ENABLE_BACKUPS” constant.
- Tweak: The Geolocation API configuration used by Trusted Devices has been moved into it’s own dedicated “Geolocation” module.
- Tweak: Move “Have I Been Pwned” integration to the Core plugin.
- Tweak: Reduce filename length and complexity for built CSS and JS files.
- Removed: The following modules have been removed: 404 Detection, Away Mode, Change Content Directory, and Multisite Tweaks.
- Removed: The following WordPress and System Tweaks have been removed: Remove Windows Live Writer Header, EditURI Header, Comment Spam, Mitigate Attachment File Traversal Attack, Protect Against Tabnapping, Filter Long URL Strings, Filter Non-English Characters, Filter Request Methods, Remove File Writing Permissions.
- Removed: The “Backup Full Database” setting has been removed from the Backups module.
- Removed: The “Require SSL”, “Front End SSL Mode”, and “SSL for Dashboard” settings have been removed from the SSL module.
- Bug Fix: Fix fatal errors when using PHP 8.
- Bug Fix: Fix infinite loop when restricting who can use App Passwords on multisite installs.
- Bug Fix: Ensure the ITSEC_Setup class does not exist before trying to load it. Display schema errors on multisite in the Network Admin.
- Bug Fix: Labels for Disable PHP Execution in Plugins and Themes were reversed.
- Bug Fix: Add missing constants to the debug page.
- Bug Fix: Remove deleted recipients when saving notifications.
- Bug Fix: Correct Site Scan statuses for scans with no issues.
- Dev Note: Modules are now based on a module.json configuration file. If you are registering custom iThemes Security module, you should update it to include a module.json file that adheres to the core/module-schema.json JSON Schema.
- Dev Note: The Network Brute Force module had it’s folder updated to “network-brute-force” from “ipcheck”.
- Dev Note: New Object Oriented API for creating Password Requirements.
- Dev Note: New Settings and Modules REST API endpoints.
- Dev Note: New RPC REST API namespace. There is no backward compatibility promise for these API endpoints.
7.9.1
- Security: Fix Hide Backend Bypass, thanks to Julio Potier for reporting the issue.
- Tweak: Add filters to short-circuit lock APIs.
- Tweak: Remove non-SSL fallbacks for Security Check Pro and Version Management.
- Bug Fix: Tweak checkbox styles.
- Bug Fix: Improved compatibility with WP Engine.
- Bug Fix: Pass the
WP_Error object to the wp_login_failed hook.
- Bug Fix: Prevent wp_no_robots deprecation warning on WordPress 5.7.
7.9.0
- Important: iThemes Security requires WordPress 5.4 or later.
- Enhancement: Add a setting for configuring the number of bans added to the server config files (.htaccess/nginx.conf).
- Enhancement: Store the time a ban was added, and the lockout module responsible for the ban.
- Enhancement: Overwrite Restrict Content Pro’s detected IP address with the IP detected by iThemes Security.
- Tweak: Disable SSL verification when performing the Security Check Loopback test. Some hosts can’t properly verify loopback requests. This verification is unnecessary in this circumstance, and disabling SSL verification aligns iThemes Security with default WordPress loopback behavior.
- Bug Fix: PHP warnings when invalid entries are stored in the WordPress Cron storage.
- Bug Fix: Update the list of tables added to wpdb.
- Bug Fix: Remove default value for text columns. This caused an issue on MySQL 8 and is unnecessary.
- Bug Fix: Missing borders in the sidebar widgets on WordPress 5.5.
- Bug Fix: Notice actions didn’t trigger when “Hide Admin Bar” is enabled.
- Bug Fix: Some users would be force to choose a strong password twice in a row.
- Bug Fix: Warning when saving the Ban Users module outside of the Settings Page without passing the legacy host_list setting.
- Bug Fix: Passwords Requirements compatibility with Restrict Content Pro.
- Bug Fix: PHP warnings that may occur when initializing default user groups on a new installation.
7.8.0
- New Feature: The new, improved WordPress Security Site Scan powered by iThemes checks if Google has detected malware and added your site to their threat list.
- Enhancement: Remove quick bans. Persist banned hosts to .htaccess or nginx.conf on an hourly schedule.
- Tweak: Cap banned hosts persisted to .htaccess or nginx.conf to the most recent 100. This number can be adjusted with the “itsec_ban_users_max_hosts_for_server_config” filter. Older banned hosts will be locked out after WordPress loads.
- Tweak: Ensure randomly generated passwords are considered strong by the Strong Passwords library.
- Tweak: Suggest a 32 character password when forcing a password change.
- Tweak: Change insensitive language to be more inclusive.
- Bug Fix: PHP warning when a user’s email address is updated outside of the user edit admin page.
- Bug Fix: Fix login interstitials on WP Engine when using a front-end login form.
- Bug Fix: PHP warning when checking opaque tokens.
- Bug Fix: PHP warning after successfully connecting a site to iThemes Sync via the login connection flow.
- Bug Fix: File Change Security Message would not appear for new installs.
7.7.1
- Bug Fix: PHP warning when evaluating password requirements.
7.7.0
- Important: iThemes Security requires PHP 5.6 or greater and WordPress 5.2 or greater.
- New Feature: Save Time Securing WordPress With User Groups!
- New Feature: Simplified connection flow when setting up iThemes Sync.
- Enhancement: Add a warning if a WordPress Salt is set to an invalid value.
- Enhancement: Include child log items in the logs list table. These are helpful for debugging issues.
- Enhancement: Improve performance of the logs page on sites with large number of log items.
- Enhancement: Check tables exist after completing a DB upgrade.
- Tweak: When logging $_SERVER, only log a snapshot of available properties.
- Bug Fix: The “Mulisite Tweaks -> Hide Updates” setting prevented auto-updates from running with WP Cron.
- Bug Fix: Backup event was not added when the WP Cron Scheduler was reset manually.
- Bug Fix: Admin Notices Popover was not being hidden when clicking outside the Popover on WP 5.3.
- Bug Fix: New Password Requirements for already created accounts were not enforced until the second login.
- Bug Fix: Update admin notices styling to be compatible with WordPress 5.4.
- Bug Fix: Periodically clear expired opaque tokens.
- Bug Fix: Don’t block registration page when “wp-signup.php” is the Hide Backend register slug.
- Bug Fix: Users with weak passwords would not be forced to change their password if the strong password requirement had been enabled after their password strength was checked.
- Bug Fix: Remove “get_magic_quotes()” call that existed for backwards compatibility with PHP versions 5.3 and earlier. This function call was causing a warning on PHP 7.4.
- Bug Fix: Warning when loading the settings page on PHP 7.4.
- Bug Fix: Warning when loading the debug page on PHP 7.4.
7.6.1
- Bug Fix: Properly notate that iThemes Security requires PHP 5.5 or greater.
7.6.0
- Breaking Change: iThemes Security requires PHP 5.5 or later.
- New Feature: iThemes Security now includes Security Check Pro to automatically and correctly determine your visitors IP addresses. Enable this scan by running Security Check and opting in to Security Check Pro or activate the Security Check Pro module in Advanced Modules. H/t Jeremy Voisin
- Enhancement: Run Security Check Pro IP Detection automatically once a day.
- Enhancement: Manually re-run Security Check Pro IP Detection from the Global Settings page.
7.5.0
- Breaking Change: iThemes Security requires PHP 5.4 or later.
- Enhancement: New Lockout Template screen.
- Enhancement: Add confirmation button to Login Interstitial Async Actions when on a different device.
- Enhancement: Add filter to “Lookup IP” link.
- Developer Note: There were significant changes to the internals of the iThemes Security Lockout API in this release. If you are using the ITSEC_Lockout class directly, all the API functions will continue to work, but will emit deprecation notices when legacy behavior is being used. Please update any integrations.
- Bug Fix: Brute Force module reporting invalid logins using an email address incorrectly.
- Bug Fix: Improve lockout compatibility with caching plugins.
- Bug Fix: Fix admin notice not being dismissed due to a REST API route that was more narrowly defined than necessary.
- Bug Fix: Admin Notices list did not refresh after dismissing a notice.
- Bug Fix: Strong Passwords zxcvbn Library was not evaluating penalty strings correctly.
- Bug Fix: Fix PHP warning if there are multiple detected proxy headers.
7.4.1
- Enhancement: New iThemes Sync Verb support for File Change.
- Tweak: Add additional information about the login attempt when calling the Network Brute Force API.
- Bug Fix: Hide Backend Bypass.
- Bug Fix: Strict Standards error during Sync request.
- Bug Fix: wp_die() if a login interstitial session fails to be created instead of throwing a fatal error.
7.4.0
- New: iThemes Security Admin Notices are now conveniently located in the new Security Messages Menu. Check your notices in the Security menu on the WordPress Admin Bar.
- Enhancement: Add Security Message when a Notification Center email fails to send.
- Enhancement: Replace Trace IP with IP Tracker Online.
- Tweak: Remove ‘DELETE’ method from “System Tweaks -> Filter Request Methods”
7.3.3
- Bug Fix: Hide backend bypass.
7.3.2
- Tweak: Allow the log description column to word break for URLs or other strings with no spaces.
- Bug Fix: Hide Backend bypass on certain Apache configurations.
- Bug Fix: Properly return error that occurs during a backup.
- Bug Fix: Regex warning on PHP 7.3 in the File Change module.
- Bug Fix: Resolve warning when a user is set to “No Role”.
7.3.1
- Enhancement: When ITSEC_DISABLE_MODULES is set, prevent hide backend from running.
- Bug Fix: Tabnapping: Apply noopener to links instead of using blankshield script when available to prevent new pop-up blocker behavior from killing the links.
7.3.0
- Enhancement: Add Per-Content SSL toggle to the upcoming Block Editor interface.
- Enhancement: Add filter to the recipients list for email notifications: “itsec_notification_{$notification}_email_recipients” and “itsec_notification_email_recipients”.
- Enhancement: Add define “ITSEC_DISABLE_TEMP_WHITELIST” to disable the Temporary IP Whitelisting for logged-in administrators.
- Enhancement: Improve redirecting after processing a login interstitial from a front-end login form.
- Enhancement: Add loopback IP detection to Security Check.
- Enhancement: Detect Server IPs in Security Check.
- Tweak: Add additional safety checks when writing to system config files. This will log a “Critical Issue” when the writing of an empty or partial config file is detected and prevented.
- Tweak: Improve File Change locking to help prevent failing scans on sites with inconsistent cron scheduling.
- Tweak: Improve “System Tweaks – Suspicious Query Strings – SQLI” to reduce false positives.
- Tweak: Improve “System Tweaks – Disable PHP” to block PHP files in apache configurations that serve files with a trailing dot.
- Tweak: Remove “Seznam Bot” from HackRepair List as it isn’t present in the latest version.
- Bug Fix: Include Hide Backend token when emailing a password reset URL.
- Bug Fix: Notification Center – Only send notifications to users with an exact role match of selected roles instead of a fuzzy match based on selected capabilities.
- Bug Fix: Error when trying to edit reusable blocks with per-post SSL enabled.
- Bug Fix: Resolve warnings on PHP 5.2.
7.2.0
- Enhancement: Allow for selecting the particular Proxy header a server is configured to use. Improve the language to indicate the importance of configuring this setting. H/t Filippo Cavallarin CEO at wearesegment.com
- Enhancement: Block access to git and svn repositories when System Tweaks -> Protect System Files is enabled.
- Tweak: Update jQuery Validation library to 1.17.0
- Bug Fix: Improve detection of blocking the File Change Scan from being scheduled if one is already being run.
- Bug Fix: Prevent infinite recursion error when trying to access directories outside of the allowed file tree.
7.1.0
- New Feature: Allow for globally setting recipients for admin-targeted notifications. All new notifications will default to the recipients in this list. Notifications can be set to use the default list or switch to a custom list.
- Enhancement: Added a setting to enable/disable the Grade Report feature of Pro.
- Tweak: Check if an IP is blacklisted on page load for compatibility with servers that cannot process server configuration level bans immediately.
- Tweak: Display a time diff until the next event on the Debug page.
- Tweak: Use Logging API for tracking Notification Center errors.
- Tweak: Register Scheduler Events whenever the plugin build changes.
- Tweak: Allow for filtering logs by any module recorded.
- Tweak: Account for 3rd-party Backup Plugin in Security Check.
- Bug Fix: 404 detection for plugins that mark is_404 later in the hook sequence.
- Bug Fix: REST API Protection blocked the Taxonomies route for all users.
- Bug Fix: Account for any CLI PHP SAPI instead of just WP-CLI in the SSL Module.
- Bug Fix: Fixed how the Grade Report enable/disable status is stored to fix admin page loading issues on some sites.
- Bug Fix: Fix serialization of closure error when a plugin registering a hook with a closure is in the boot-up stack and the notification center is triggered too early in the cycle.
7.0.4
- Enhancement: Add mitigation for the WordPress Attachment File Traversal and Deletion vulnerability.
- Tweak: Fire a WordPress action whenever settings are updated.
- Bug Fix: Improved input sanitization on the logs page to prevent triggering warnings.
7.0.3
- Security Fix: Fixed SQL injection vulnerability in the logs page. Note: Admin privileges are required to exploit this vulnerability. Thanks to Çlirim Emini, Penetration Tester at sentry.co.com, for reporting this vulnerability.
- Bug Fix: Provide default values for enabled requirements.
7.0.2
- Enhancement: Add UI to cancel in progress File Scan.
- Enhancement: Add basic admin debug page to help diagnosing and resolving issues. Particularly with the events.
- Enhancement: Add debug settings JSON editor.
- Enhancement: Continually evaluate password strength for users instead of only during registration.
- Enhancement: Introduce Password Requirements module for managing and enforcing password requirements.
- Bug Fix: Accessing password requirement settings would not resolve properly in some instances.
- Bug Fix: Away Mode would not lock out users who were already logged-in during the “away” period.
- Bug Fix: Enforce the Strong Passwords requirement during Security Check.
- Bug Fix: Ensure scheduling lock is cleared by the Cron Scheduler when not proceeding with running events.
- Bug Fix: If a password requirement has been disabled or is no longer available, don’t consider the password as needing a change.
- Bug Fix: Only hide “Acknowledge Weak Password” checkbox if the user was not allowed to use a weak password.
- Bug Fix: Password strength would not be evaluated if password was set using custom PHP or CLI commands.
- Bug Fix: Prevent File Change from getting stuck in an infinite rescheduling loop on the first step.
- Bug Fix: Remove distributed storage table on uninstall.
- Tweak: Don’t write to the tracked files setting if the file hash has not changed.
- Tweak: If no last password change date is recorded for the user, treat their registration date as the last change date.
7.0.1
- Bug Fix: Fixed an “Uncaught Error: Call to undefined function esc_like()” error that could occur when exporting or erasing personal data.
- Bug Fix: Skip recovery if File Change storage is empty.
7.0.0
- New Feature: Added support for the new WordPress privacy features.
- Enhancement: Added minimal API for adding additional entries to the Security admin menu.
- Enhancement: File Change Scan uses a new batching mechanism to prevent crashing on hosts but still generating only one report per-day.
- Enhancement: Introduce Distributed Storage framework for reducing the amount of data stored in the WordPress options table. This should improve performance for large sites using File Change.
- Enhancement: Introduced Login Interstitial framework to consolidate code between Password Requirements & Two Factor.
- Bug Fix: Added ability to show object data for classes that are not loaded to the Logs page.
- Bug Fix: Changed the rules generated by the Filter Suspicious Query Strings feature in order to avoid blocking privacy export/erasure request confirmations.
- Bug Fix: Ensure all users with the
manage_options capability are available when selecting contacts in the Notification Center.
- Bug Fix: Fix clearing or previous file scans results.
- Bug Fix: Fix warnings on debug file change log items.
- Bug Fix: Fixed logging system references to “fatal-error” that should be “fatal”.
- Bug Fix: Improve File Change recovery system on high-traffic websites.
- Bug Fix: Improve clearing of previous File Change file hashes.
- Bug Fix: Improved detection of REST API requests on sites without a home dir.
- Bug Fix: Internal links to a filtered logs page.
- Bug Fix: Prevent PHP warning about converting an array to a string when adding notification data.
- Bug Fix: Prevent PHP warning when completing database backups that are not emailed to any recipients.
- Bug Fix: Properly enforce strong passwords when on the WP Login Reset Password page.
- Bug Fix: Resolve warnings when upgrading file change settings.
- Minor: File Scan “chunk” option is removed.
- Minor: Make recovering file scan log smaller.
- Minor: Page Load Scheduler: Unschedule single events before running them. This mirrors the behavior of the WP Cron scheduler.
- Minor: Security Digest now includes all lockouts that have occurred since the last email.
- Minor: Shrink storage size of file scans.
- Minor: Specifying a manual file scan list has been removed.
- Minor: Track raw memory used by the file change scanner as well.
- Minor: Updated list of File Change excluded file types to include more media extensions.
- Misc: Added comment to prevent Tide from marking the plugin as not compatible with PHP 5.3.
- Tweak: Add description for File Change recovery related logs.
- Tweak: Don’t report removed files if the removal is caused by a new file extension being excluded.
- Tweak: File Change: Move “latest_changes” entry to a separate storage bucket to improve performance on large sites.
- Tweak: File Change: Only scan a maximum of 10 plugins in a single chunk.
6.9.2
- Bug Fix: Fixed situation that could cause lockout notifications being sent for whitelisted IPs.
- Bug Fix: Fixed issue where saving Global Settings would be blocked by an unwritable “Path to Log Files” path when the “Log Type” is set to “Database Only”.
- Bug Fix: Fixed issue that prevented log database entries from purging and log file entries from rotating on a schedule.
6.9.1
- Security Fix: Fixed display of unescaped data on logs page.
- Enhancement: The logging …